The Brooklyn cult hero in the flesh A live performance in the UK from Brooklyn cult electronic hero Oneohtrix Point Never is a rare treat indeed. The last time we remember him headlining a show in the capital was way back in 2018, when he played the Barbican centre in support of his Age Of […]
“Test files” associated with the XZ Utils backdoor have made their way to a Rust crate known as liblzma-sys, new findings from Phylum reveal. liblzma-sys, which has been downloaded over 21,000 times to date, provides Rust developers with bindings to the liblzma implementation, an underlying library that is part of the XZ Utils data compression […]
The security issue could lead to the exfiltration of process memory addresses, which could help attackers bypass protection mechanisms like Address Space Layout Randomization (ASLR).
Apple has updated its documentation related to its warning system for mercenary spyware threats, now specifying that it alerts users when they may have been individually targeted by such attacks. The revision points out companies like NSO Group, known for developing surveillance tools like Pegasus, which state actors often use for targeted attacks on individuals […]
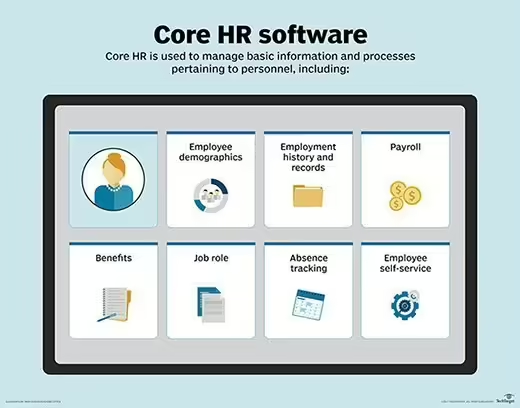
What is core HR (core human resources)? Core HR (core human resources) is an umbrella term that refers to the basic tasks and functions of an HR department as it manages the employee lifecycle. This includes the basic data captured about employees and the software used to manage basic HR processes, from recruitment to offboarding. […]
During the “Swords of Iron War” against Hamas terrorists, Iranian threat actors increased the intensity of their “hack and leak” fake hacktivist operations against Israeli companies in the private sector. This blog post highlights some of the recent attacks conducted and provides an analysis of “DarkBeatC2,” the latest C2 framework in MuddyWater’s arsenal. Executive Summary […]
Microsoft fixed two zero-day bugs exploited in malware attacks Pierluigi Paganini April 11, 2024 Microsoft addressed two zero-day vulnerabilities (CVE-2024-29988 and CVE-2024-26234) actively exploited by threat actors to deliver malware Microsoft addressed two zero-day vulnerabilities, tracked as CVE-2024-29988 and CVE-2024-26234, that threat actors are exploiting to deliver malware. Microsoft Patches Tuesday security updates for April […]
Palo Alto Networks fixed multiple DoS bugs in its firewalls Pierluigi Paganini April 11, 2024 Palo Alto Networks fixed several vulnerabilities in its PAN-OS operating system, including 3 issues that can trigger a DoS condition on its firewalls. Palo Alto Networks released security updates to address several high-severity vulnerabilities in its PAN-OS operating system. The […]
Attackers are adept at identifying and exploiting the most cost-effective methods of compromise, highlighting the critical need for organizations to implement asset identification and understand their assets’ security posture in relation to the whole estate. Instead of asking, “Are we exposed?” organizations should ask, “How exposed are we?” To understand this question, businesses must implement […]
- 1
- 2