The new Atomic variant uses Python and Apple Script code to target browser and system files, obtain user account passwords, and identify sandbox or emulator execution. Bitdefender researchers have discovered a new variant of the AMOS Stealer (or Atomic Stealer), one of the most prevalent threats for macOS users in the last year. According to […]
System monitoring tools, like Glances, offer data center administrators two advantages: Ensure the system is not overwhelmed and provide preventive maintenance. Today’s OSes provide many tools to make monitoring data centers easier. Common performance monitoring utilities include top and htop for Linux, top for macOS, and Task Manager and Resource Monitor for Windows. Glances is […]
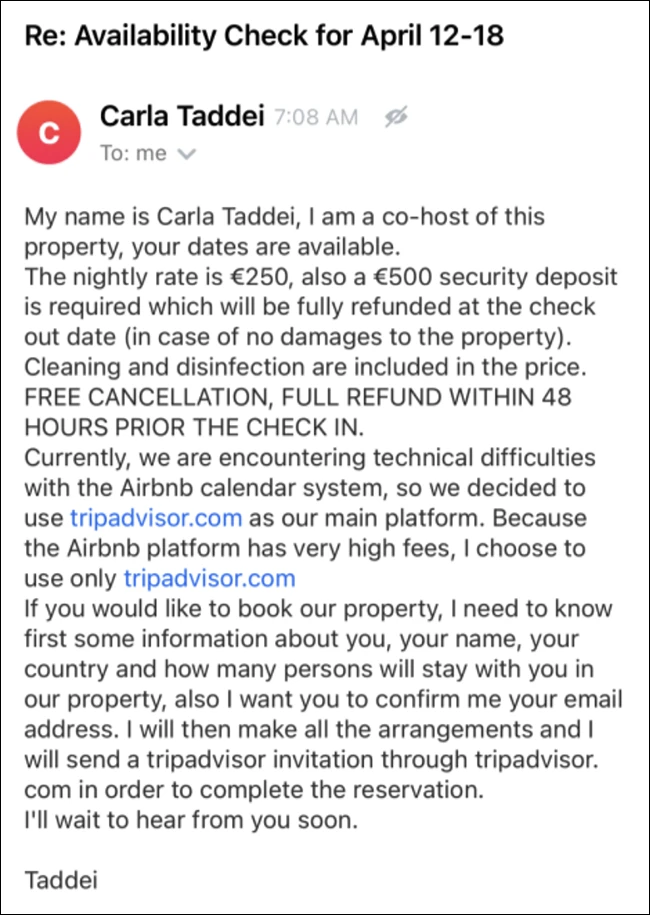
Scammers on Airbnb are faking technical issues and citing higher fees to get users to a spoofed Tripadvisor website and steal their money. The Airbnb scam Malwarebytes researchers came across the Airbnb scam when trying to book an apartment through the platform. The owner/scammer noted in the listing that those interested in booking the property […]
Listen to the article 4 min This audio is auto-generated. Please let us know if you have feedback. Dive Brief: The September cyberattack that exposed all of Okta’s customer support system clients did not have a material impact on the company’s financial performance in the fiscal 2024 fourth quarter, which ended Jan. 31, executives said […]
The malicious packages were disguised as legitimate Python packages, and although they have been removed from PyPI, they were downloaded over 3,000 times, compromising thousands of systems.
OffSec has released Kali Linux 2024.1, the latest version of its popular penetration testing and digital forensics platform. The new version comes with new tools, a fresh look (themes, wallpapers and icons for Kali and Kali Purple), a new image viewer for the Gnome desktop and a usability enhancement to the Xfce desktop (the ability […]
Personal data of victims is collected through registration forms on fake investment platforms, and the actor tracks user information while preventing revisits from crawlers and security vendors.
The exploit allowed Lazarus to enhance its FudModule rootkit, enabling it to evade detection and disable security protections. Additionally, a previously undocumented remote access trojan (RAT) used by Lazarus was discovered.
Mar 01, 2024NewsroomRootkit / Threat Intelligence The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in Ivanti Connect Secure and Ivanti Policy Secure gateways, noting that the Integrity Checker Tool (ICT) can be deceived to provide a false sense of security. “Ivanti ICT […]