Re-writing Heist-story “We’ve always really loved being a part of it and hosting part of ADE as locals,” says Maarten Smeets, one half of the Amsterdam-based duo Dam Swindle. “Being a good host, telling people the best places to go – and the bars to avoid.” Smeets, who actually lives just outside the city, because, […]
The efforts of the International Committee of the Red Cross (ICRC) to establish rules of engagement to combatants in a cyberwar should be applauded internationally, even if adherence is likely to be limited. The ICRC recently released a set of rules for civilian hackers involved in conflicts to follow in order to clarify the line between civilians […]
The attacks involve the use of weaponized documents with malicious macros that create a reverse shell, allowing the attackers to gain control over the compromised systems.
The BlackCat ransomware group has reportedly targeted Ho Chi Minh City Energy Company, a subsidiary of Vietnam Electricity. The alleged EVNHCMC data breach has raised concerns, prompting the hacker group ALPHV to threaten to report the incident to the Vietnam Department of Energy. The situation is unfolding, with 84 samples from the Vietnam Electricity data […]
The exposed API tokens had write permissions, allowing attackers to modify files in account repositories and potentially manipulate existing models, posing a significant threat to organizations and their applications.
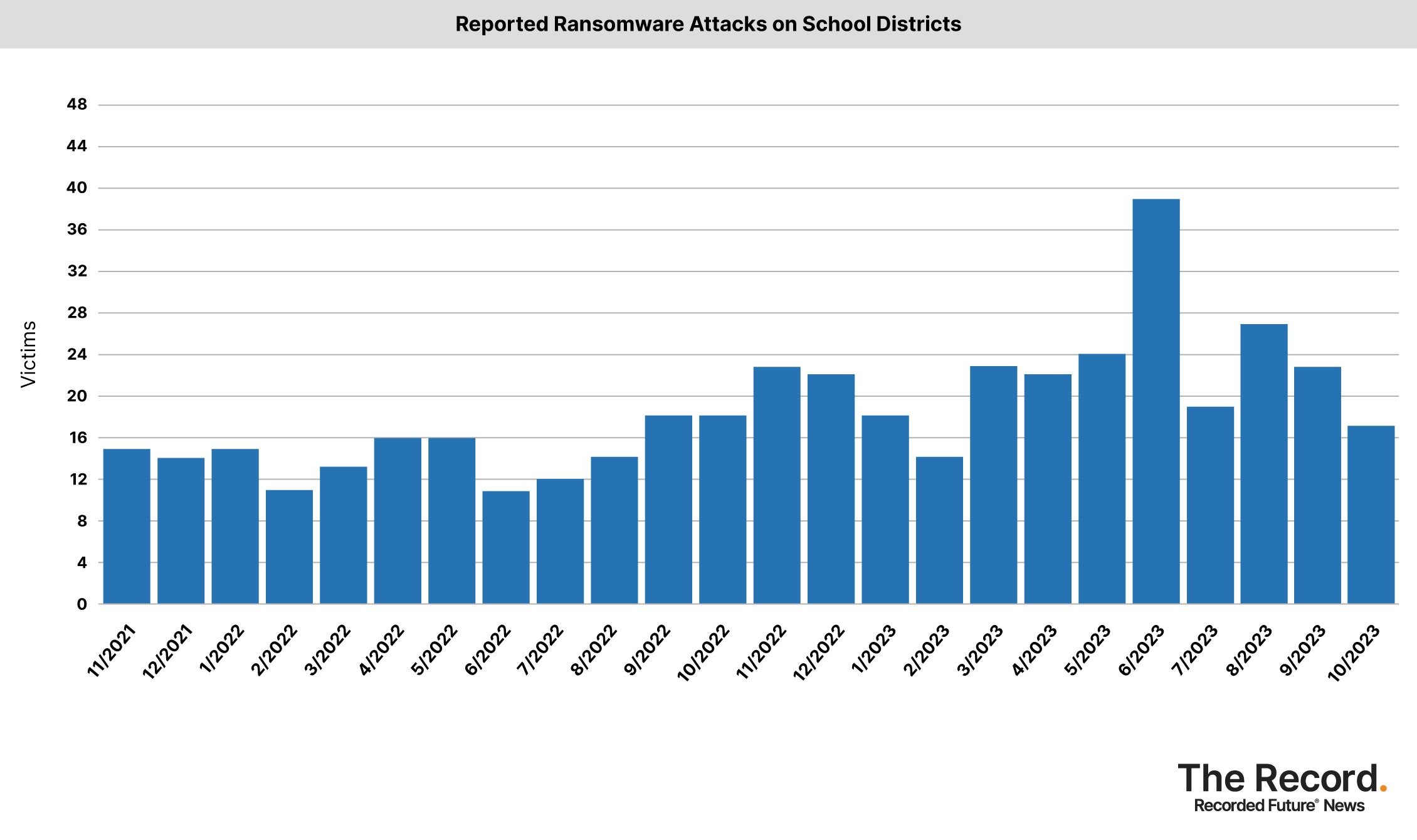
DePauw University warned students this week that their personal information may have been accessed by hackers who attacked the school. The school newspaper reported that on November 27, current and prospective students were sent letters notifying them of a data leak and providing them with one year of free identity protection services. The liberal arts […]
Summary A new P2Pinfect variant compiled for the Microprocessor without Interlocked Pipelined Stages (MIPS) architecture has been discovered This demonstrates increased targeting of routers, Internet of Things (IoT) and other embedded devices by those behind P2Pinfect The new sample includes updated evasion mechanisms, making it more difficult for researchers to dynamically analyse These include Virtual […]
Dec 04, 2023NewsroomEncryption / Technology New research has unearthed multiple novel attacks that break Bluetooth Classic’s forward secrecy and future secrecy guarantees, resulting in adversary-in-the-middle (AitM) scenarios between two already connected peers. The issues, collectively named BLUFFS, impact Bluetooth Core Specification 4.2 through 5.4. They are tracked under the identifier CVE-2023-24023 (CVSS score: 6.8) and […]
Fortune-telling website WeMystic exposes 13M+ user records Pierluigi Paganini December 02, 2023 WeMystic, a website on astrology, numerology, tarot, and spiritual orientation, left an open database exposing 34GB of sensitive data about the platforms’ users. Telling the future is a tricky business, and failure to foretell your own mishaps doesn’t help. The content platform WeMystic […]