HUMAN Satori Threat Intelligence Alert: Account Takeover Attacks Use ScrubCrypt to Deploy RedLine Stealer Malware
Researchers: Gabi Cirlig, Adam Sell, Arik Atar
ScrubCrypt is an obfuscation tool threat actors use to help slip malware past antivirus software, allowing them to launch attacks that might otherwise be stopped. HUMAN’s Satori Threat Intelligence Team recently uncovered a new build of ScrubCrypt available for sale in underground communities and used in attacks on HUMAN customers. Satori researchers reverse engineered the attack to reveal the new ScrubCrypt build’s workings.
In an attack on a HUMAN customer, ScrubCrypt was used to deliver RedLine Stealer—a known cybersecurity attack capable of credential and cryptocurrency wallet exfiltration—with the intention of carrying out account takeover and account fraud attacks on the customer’s users.
HUMAN customers are protected from account takeover and account fraud attacks centered on stealer malware, including those using this iteration of ScrubCrypt.
RedLine Stealer is a piece of malware that targets end users with the goal of compromising accounts through stealing cookies, browser login data, and locally-stored login information. The malware receives commands from a C2 server to search for various items and patterns (username/password, cryptocurrency wallet formation, certain phrases in text files, etc.) and upload any matched data from the infected device to the attacker’s infrastructure.
This allows threat actors to conduct account takeover and account fraud attacks by logging in with the stolen credentials or reusing the cookies stolen from the browser. RedLine Stealer is, essentially, an all-in-one solution for cookie and login stealing. RedLine Stealer has been extensively described by the cybersecurity community, but remains a threat nonetheless, particularly when paired with obfuscation tools like ScrubCrypt that help sneak RedLine Stealer past the AV software intended to detect it.
For a detailed analysis of RedLine Stealer, please visit any of the resources linked in the Acknowledgements section of this report.
This report will explore the attack surfaced by HUMAN from two perspectives: how the new build of ScrubCrypt works and how HUMAN found it. The former will share the results of the Satori team’s reverse engineering and threat intelligence of the sample, while the latter will examine the marketplaces on which it’s sold and how threat actors disseminate it to begin ATO or account fraud attacks.
Buying ScrubCrypt
ScrubCrypt’s “marketing” promotes the add-on to threat actors as an easy way to obfuscate executable files by converting them into batch files.
Banner ad promoting ScrubCrypt
Source: Satori Threat Intelligence and Research Team
This conversion—from executable file into batch file—enables threat actors to slip attacks past many preventative measures that might otherwise identify them. Many email providers and messaging platforms have safeguards that prevent executable files from showing up as attachments in a primary (non-spam) inbox. And .bat files don’t trigger antivirus software’s detection in the same way executable files might.
The new ScrubCrypt build was sold to threat actors on a small handful of dark web marketplaces, including Nulled Forum, Cracked Forum, and Hack Forums.
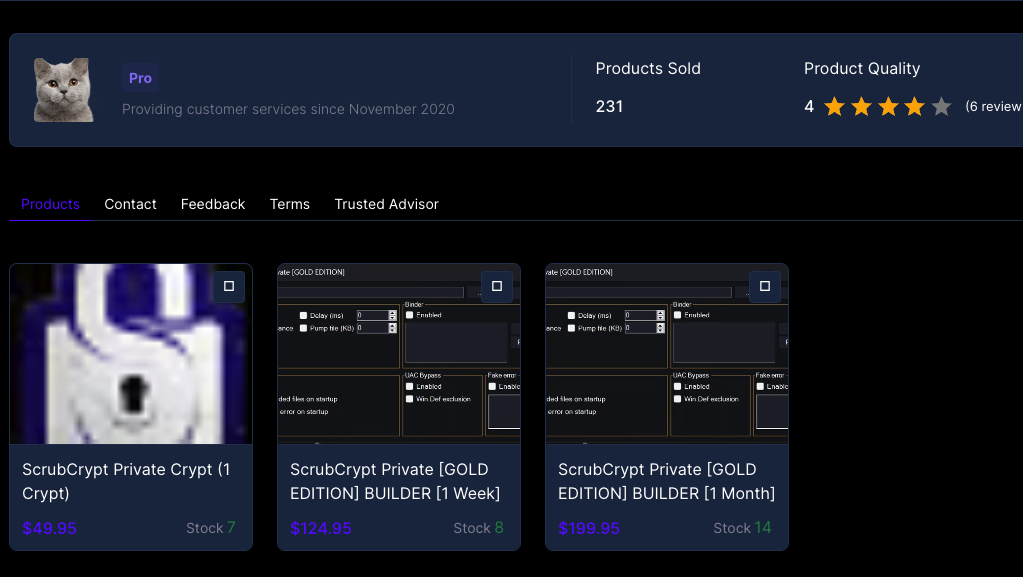
ScrubCrypt sold on a dark web marketplace
Source: Satori Threat Intelligence and Research Team
In an effort to evade law enforcement, the website selling and hosting this new ScrubCrypt build is registered and hosted in Russia, outside the reach of US and EU agencies.
Details of one registrar for the new ScrubCrypt build
Source: Satori Threat Intelligence and Research Team
The C2 server sending instructions and receiving the stolen credentials from the associated RedLine Stealer sample, however, is hosted by an American provider of data center proxies and virtual servers. Satori researchers believe this is in an effort by the threat actors to avoid certain firewall protections by having the malware phone home to a server located within the country of the target.
.bat file
The first stage of the infection is a .bat file downloaded to a victim’s device, often as the result of social engineering. (For example, a link shared from a compromised account to another account via a direct-messaging system, or spread through an email from the mail provider on a compromised device.)
This .bat file carries a base64-encoded payload and is peppered throughout with nonsensical repeating strings:
Obfuscated .bat file
Source: Satori Threat Intelligence and Research Team
These strings are intended to help obfuscate the payload, but after removing them and decrypting the AES-encrypted file, the payload is revealed to be compressed gzip data.
Obfuscated .bat file with gibberish highlighted
Source: Satori Threat Intelligence and Research Team
Deobfuscated .bat file
Source: Satori Threat Intelligence and Research Team
gzip files, like the extension suggests, are unzippable, compressed files. Extracting the data stream reveals an obfuscated .NET executable file, the next stage of the infection.
.NET executable
The code of the .NET executable file is heavily obfuscated, as seen in the image below.
Obfuscated .NET intermediary layer
Source: Satori Threat Intelligence and Research Team
Satori researchers used certain functions from the obfuscated code and an open-source deobfuscation tool called d4dot to get a clearer look at the .NET payload.
Deobfuscated .NET intermediary layer
Source: Satori Threat Intelligence and Research Team
In the deobfuscated payload, Satori researchers observed that the file loads an embedded resource called P. The sample then deobfuscates P using an XOR cipher with a key embedded in the .NET executable to get the final Windows executable payload. In this research, the final payload was RedLine Stealer, though other payloads can be encrypted and slipped past antivirus protections with ScrubCrypt:
Embedded payload within intermediary layer
Source: Satori Threat Intelligence and Research Team
Decryption key for final payload
Source: Satori Threat Intelligence and Research Team
The attack targeted one HUMAN customer through its direct messaging platform. This platform has been targeted by threat actors using RedLine Stealer before, but this was the first instance incorporating this build of ScrubCrypt.
This customer’s users were protected from the impacts of the RedLine Stealer payload by HUMAN’s Account Takeover Defense and Account Fraud Defense solutions. Account Takeover Defense identified automated and suspicious credential stuffing and brute force attempts, blocking the threat actors attempting these attacks from gaining access to user accounts. Account Fraud Defense identified compromised accounts and neutralized them, alerting the targeted platform and victimized users of the breach.
Both solutions can force compromised users to change their user credentials, confirm identity through 2FA, or other customizable results.
This story is an example of the importance of staying ahead of adversaries: as each new build of malware like RedLine Stealer or obfuscation tools like ScrubCrypt are unearthed and built into antivirus protections, threat actors go back to the drawing board to start designing the next build.
This attack is emblematic of an alternative means of compromising accounts. Rather than relying on leaked/stolen credentials followed by a brute-force attack, some threat actors prefer a malware-based approach to account fraud using stealers like the RedLine Stealer payload in this attack.
HUMAN recommends organizations (particularly those with direct/private messaging capabilities native to their user platforms) deploy protections that detect and mitigate cookie-stealing attacks and that flag users with credentials leaked or stolen in other threats.
The Satori Threat Intelligence Team would like to acknowledge the work of the following cybersecurity organizations, each of which has published information about RedLine Stealer:
(in no particular order)
Malpedia also has a lengthy list of analyses of RedLine Stealer. The Satori team recommends reviewing these resources for greater understanding of RedLine Stealer.
Additionally, the Satori team would like to acknowledge the work of cybersecurity organizations and researchers toward earlier versions of ScrubCrypt:
Malpedia also has a list of analyses of earlier iterations of ScrubCrypt.
SHA 256 hashes of RedLine Stealer payload with ScrubCrypt obfuscation:
| SHA256 | Type |
| 17fbe04f41d80d15ac5418cbe580e516a157aa0ce02495660feb653f658b43b8 | encryption software |
| fc286589f4422acb28fea5191fb05e9c9b177d4fd5b3795f0acfdee4ccafffac | evasion layer |
| e2cc0ab598ae05e5665ebf621673fb8fbbd6a7d5bbd5cc4b43bda52bc77e8379 | final payload |
IP address of C2 server: 23.230.159[.]97:38633
List of what RedLine Stealer can exfiltrate:
| Login data | Crypto wallet data | VPN login data |
| Chrome saved passwords | YoroiWallet | NordVPN |
| Firefox saved passwords | Tronlink | OpenVPN |
| Opera saved passwords | NiftyWallet | ProtonVPN |
| Auto-fill content | Metamask | FileZilla |
| Browser cookies | MathWallet | |
| Discord login data | Coinbase | |
| Telegram login data | BinanceChain | |
| Discord chat logs | BraveWallet | |
| Telegram chat logs | GuardaWallet | |
| Steam account (SSFN) | EqualWallet | |
| JaxxxLiberty | ||
| BitAppWallet | ||
| iWallet | ||
| Wombat | ||
| AtomicWallet | ||
| MewCx | ||
| GuildWallet | ||
| SaturnWallet | ||
| RoninWallet | ||
| TerraStation | ||
| HarmonyWallet | ||
| Coin98 Wallet | ||
| TonCrystal | ||
| KardiaChain | ||
| Phantom | ||
| Oxygen | ||
| PaliWallet | ||
| BoltX | ||
| LiqualityWallet | ||
| XdefiWallet | ||
| NamiWallet | ||
| Maiar DeFi Wallet | ||
| Authenticator |

