Cybercriminals Using New ASMCrypt Malware Loader Flying Under the Radar
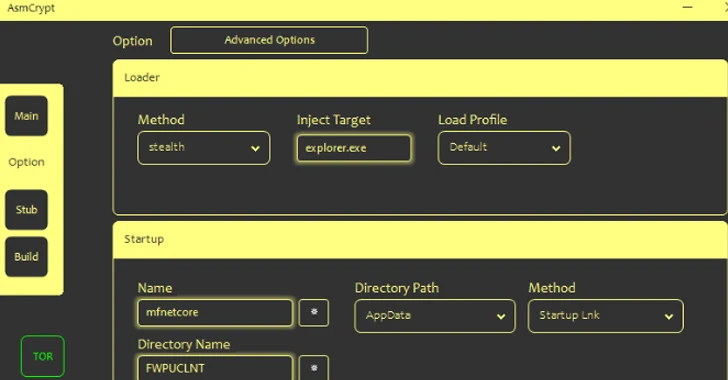
Threat actors are selling a new crypter and loader called ASMCrypt, which has been described as an “evolved version” of another loader malware known as DoubleFinger.
“The idea behind this type of malware is to load the final payload without the loading process or the payload itself being detected by AV/EDR, etc.,” Kaspersky said in an analysis published this week.
DoubleFinger was first documented by the Russian cybersecurity company, detailing infection chains leveraging the malware to propagate a cryptocurrency stealer dubbed GreetingGhoul to victims in Europe, the U.S., and Latin America.
ASMCrypt, once purchased and launched by the customers, is designed to establish contact with a backend service over the TOR network using hard-coded credentials, thereby enabling the buyers to build payloads of their choice for use in their campaigns.
“The application creates an encrypted blob hidden inside a .PNG file,” Kaspersky said. “This image must be uploaded to an image hosting site.”
Loaders have become increasingly popular for their ability to act as a malware delivery service that can be utilized by other threat actors to gain initial access to networks for conducting ransomware attacks, data theft, and other malicious cyber activities.

This includes players new and established, such as Bumblebee, CustomerLoader, and GuLoader, which have been used to deliver a variety of malicious software. Interestingly, all payloads downloaded by CustomerLoader are dotRunpeX artifacts, which, in turn, deploys the final-stage malware.
“CustomerLoader is highly likely associated with a Loader-as-a-Service and used by multiple threat actors,” Sekoia.io said. “It is possible that CustomerLoader is a new stage added before the execution of the dotRunpeX injector by its developer.”
Bumblebee, on the other hand, reemerged in a new distribution campaign after a two-month hiatus towards the end of August 2023 that employed Web Distributed Authoring and Versioning (WebDAV) servers to disseminate the loader, a tactic previously adopted in IcedID attacks.
“In this effort, threat actors utilized malicious spam emails to distribute Windows shortcut (.LNK) and compressed archive (.ZIP) files containing .LNK files,” Intel 471 said. “When activated by the user, these LNK files execute a predetermined set of commands designed to download Bumblebee malware hosted on WebDAV servers.”
The loader is an updated variant that has transitioned from using the WebSocket protocol to TCP for command-and-control server (C2) communications as well as from a hard-coded list of C2 servers to a domain generation algorithm (DGA) that aims to make it resilient in the face of domain takedown.
In what’s a sign of a maturing cybercrime economy, threat actors previously assumed to be distinct have partnered with other groups, as evidenced in the case of a “dark alliance” between GuLoader and Remcos RAT.
While ostensibly advertised as legitimate software, a recent analysis from Check Point uncovered the use of GuLoader to predominantly distribute Remcos RAT, even as the former is now being sold as a crypter under a new name called TheProtect that makes its payload fully undetectable by security software.
Fight AI with AI — Battling Cyber Threats with Next-Gen AI Tools
Ready to tackle new AI-driven cybersecurity challenges? Join our insightful webinar with Zscaler to address the growing threat of generative AI in cybersecurity.
“An individual operating under the alias EMINэM administers both websites BreakingSecurity and VgoStore that openly sell Remcos and GuLoader,” the cybersecurity firm said.
“The individuals behind these services are deeply entwined within the cybercriminal community, leveraging their platforms to facilitate illegal activities and profit from the sale of malware-laden tools.”
The development comes as new versions of an information stealing malware referred to as Lumma Stealer have been spotted in the wild, with the malware distributed via a phony website that mimics a legitimate .DOCX to .PDF site.
Thus, when a file is uploaded, the website returns a malicious binary that masquerades as a PDF with a double extension “.pdf.exe” that, upon execution, harvests sensitive information from infected hosts.
It’s worth noting that Lumma Stealer is the latest fork of a known stealer malware named Arkei, which has evolved into Vidar, Oski, and Mars over the past couple of years.
“Malware is constantly evolving, as is illustrated by the Lumma Stealer, which has multiple variations with varying functionality,” Kaspersky said.