SideCopy Exploiting WinRAR Flaw in Attacks Targeting Indian Government Entities
The Pakistan-linked threat actor known as SideCopy has been observed leveraging the recent WinRAR security vulnerability in its attacks targeting Indian government entities to deliver various remote access trojans such as AllaKore RAT, Ares RAT, and DRat.
Enterprise security firm SEQRITE described the campaign as multi-platform, with the attacks also designed to infiltrate Linux systems with a compatible version of Ares RAT.
SideCopy, active since at least 2019, is known for its attacks on Indian and Afghanistan entities. It’s suspected to be a sub-group of the Transparent Tribe (aka APT36) actor.
“Both SideCopy and APT36 share infrastructure and code to aggressively target India,” SEQRITE researcher Sathwik Ram Prakki said in a Monday report.
Earlier this May, the group was linked to a phishing campaign that took advantage of lures related to India’s Defence Research and Development Organization (DRDO) to deliver information-stealing malware.
Since then, SideCopy has also been implicated in a set of phishing attacks targeting the Indian defense sector with ZIP archive attachments to propagate Action RAT and a new .NET-based trojan that supports 18 different commands.
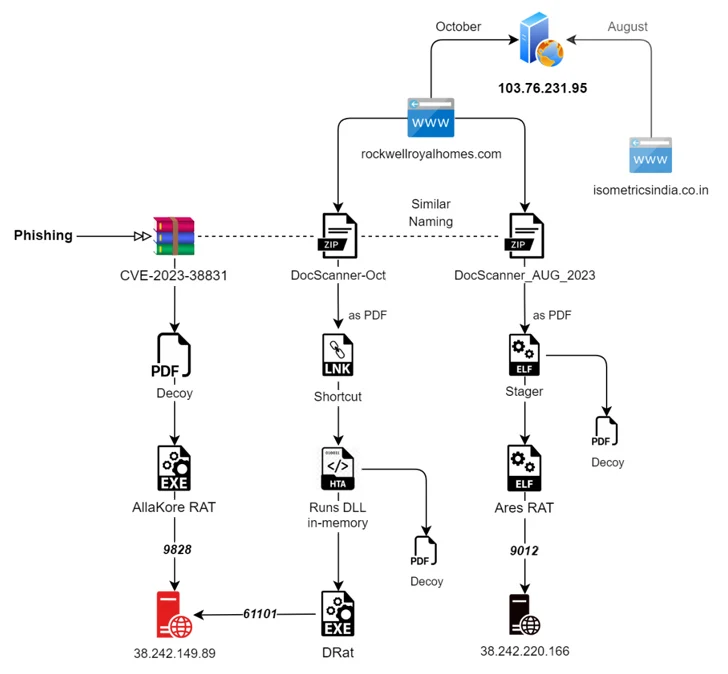
The new phishing campaigns detected by SEQRITE entail two different attack chains, each targeting Linux and Windows operating systems.
The former revolves around a Golang-based ELF binary that paves the way for a Linux version of Ares RAT that’s capable of enumerating files, taking screenshots, and file downloading and uploading, among others.
The second campaign, on the other hand, entails the exploitation of CVE-2023-38831, a security flaw in the WinRAR archiving tool, to trigger the execution of malicious code, leading to the deployment of AllaKore RAT, Ares RAT, and two new trojans called DRat and Key RAT.
“[AllaKore RAT] has the functionality to steal system information, keylogging, take screenshots, upload & download files, and take the remote access of the victim machine to send commands and upload stolen data to the C2,” Ram Prakki said.
DRat is capable of parsing as many as 13 commands from the C2 server to gather system data, download and execute additional payloads, and perform other file operations.
The targeting of Linux is not coincidental and is likely motivated by India’s decision to replace Microsoft Windows with a Linux flavor called Maya OS across government and defense sectors.
“Expanding its arsenal with zero-day vulnerability, SideCopy consistently targets Indian defense organizations with various remote access trojans,” Ram Prakki said.
“APT36 is expanding its Linux arsenal constantly, where sharing its Linux stagers with SideCopy is observed to deploy an open-source Python RAT called Ares.”