Raven: Open-source CI/CD pipeline security scanner – Help Net Security
Raven (Risk Analysis and Vulnerability Enumeration for CI/CD) is an open-source CI/CD pipeline security scanner that makes hidden risks visible by connecting the dots across vulnerabilities woven throughout the pipeline that, when viewed collectively, reveal a much greater risk than when assessed as one-off CVEs.

Raven boosts the ability of security teams to implement secure software development practices, enabling them to work more strategically with DevOps teams while maturing their organization’s ASPM capabilities.
How Raven works
Initially focused on GitHub, Raven scans GitHub workflows and breaks them into individual components. These components are then inserted into a Neo4j database as distinct types of nodes, with relationships established between them. This allows for effortless scanning and identification of vulnerabilities in workflows.
Raven utilizes a knowledge base built over the course of more than a year of comprehensive research into GitHub Actions by the Cycode research team. Throughout this period, data was gathered from a wide spread of systems, thousands of projects, and multiple configurations.

Two workflows vulnerable to code injection via pull request titles detected in the database
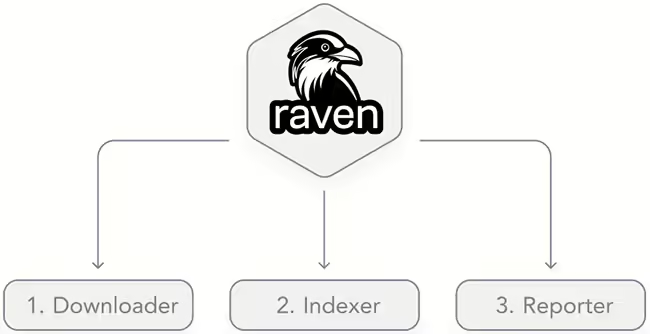
Raven components
Raven consists of the following components:
Downloader: To download workflows and actions necessary for analysis. Workflows can be downloaded for a specified organization or for all repositories, sorted by star count. Performing this step is a prerequisite for analyzing the workflows.
Indexer: To digest the downloaded data into a graph-based Neo4j database. This process involves establishing relationships between workflows, actions, jobs, steps, etc.
Query Library: A library of predefined queries based on research conducted by the community.
Report: Raven has a simple way of reporting suspicious findings. For example, it can be incorporated into the CI process for pull requests and run there.
Raven is available for free on GitHub.

More open-source tools to consider: