Ransomware realities in 2023: one employee mistake can cost a company millions
Ransomware realities in 2023: one employee mistake can cost a company millions

What is the impact of ransomware on organizations? One employee’s mistake can cost a company millions of dollars.
Studies show that human error is the root cause of more than 80% of all cyber breaches, whether malicious or unintended. The recent debilitating cyberattacks on casino and resort giants MGM and Caesars are no exception. How can just one employee mishap cost a company millions?
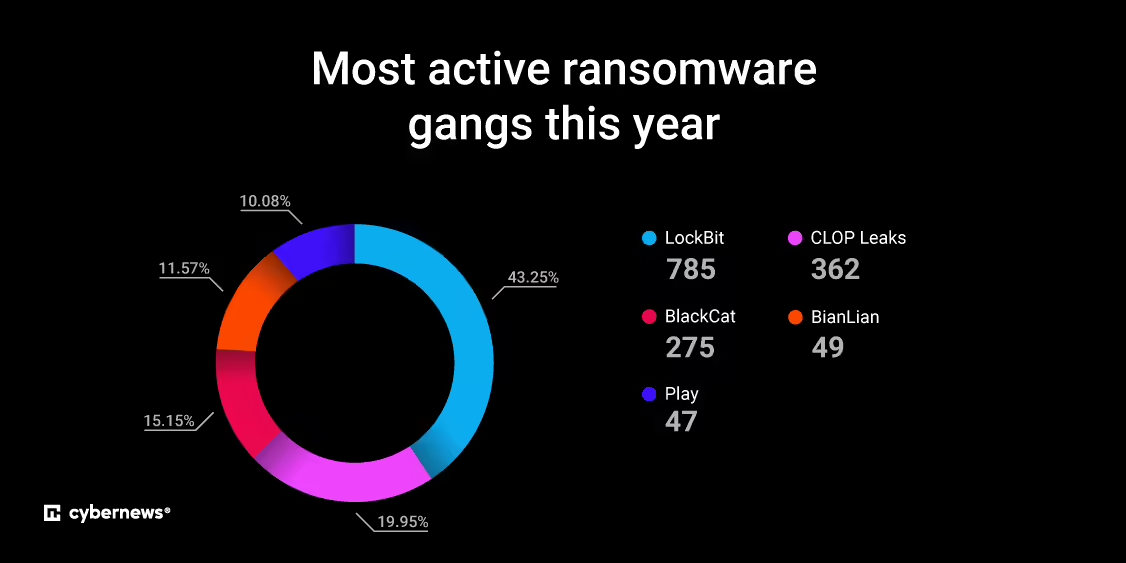
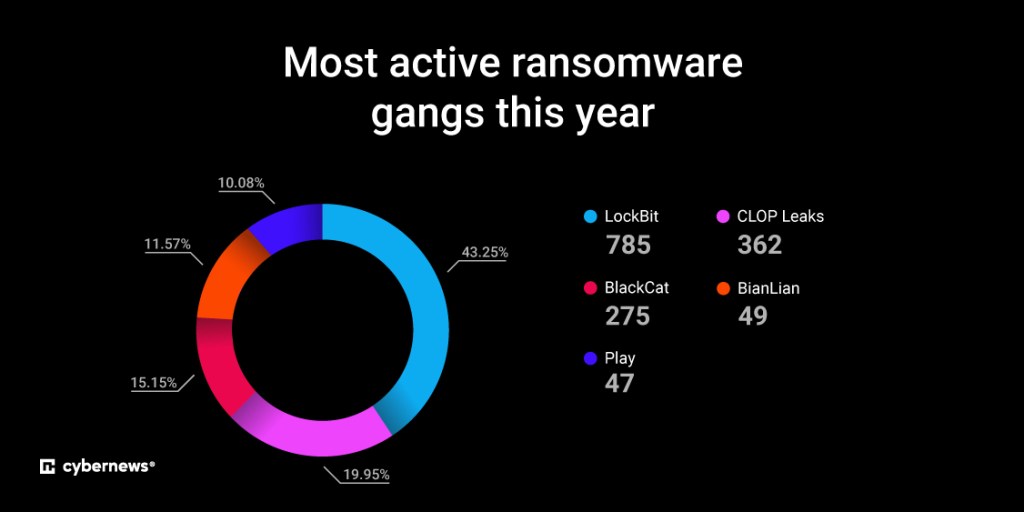
According to Statista.com, the impact of cybercrime is expected to reach almost $13 trillion this year. Furthermore, it’s estimated that this sum will increase to nearly $24 trillion by 2027. Based on Ransomlooker, a free Cybernews tool for monitoring the dark web and other hidden areas of the internet, 64% of organizations have already suffered from a ransomware attack.
This is happening despite an exponential increase in organizational cyber training over the past decade. Not to mention the heightened cyber awareness and risk mitigation across businesses and industries. With 85% of campaigns targeting victims with phishing emails containing malicious links, another form of a social engineering attack, education and cyber vigiliance remain a high priority.
Why should employers educate employees about cyber security?
MGM has revealed that the September 11th attack – which forced an entire system shutdown, impacting all guest services and emptying casino floors for nearly a week – will cost the company upwards of $100 million in 3rd quarter profits. Caesars International allegedly forked over a $15 million ransom to the attackers to keep business operations afloat.
The ransom gangs behind the attacks – Scattered Spider and ALPHV/BlackCat – used the same social engineering tactic to gain unauthorized access to MGM’s and Caesars’ network systems. This method was identified as vishing – a voice-based phishing attack.
Caesars claimed that it had “identified suspicious activity in its information technology network resulting from a social engineering attack on an outsourced IT support vendor used by the Company.” The MGM attacks were almost identical to the social engineering attacks on Caesars, which targeted a third-party IT help desk.
The ease and success of these social engineering attacks illustrate how just one employee mishap can cost a company millions. Social engineering encompasses various methods that attackers can utilize to trick an employee into giving up sensitive information, allowing access to otherwise secure networks.
For large businesses, those costs may be a drop in the ocean. Still, for many small and mid-sized companies, the financial and reputational ramifications from a cyberattack can be devastating. Statistics have shown that nearly 60% of small businesses that suffer a significant breach are forced to shut down within the same year. Furthermore, based on findings from the Ransomlooker tool, 45% of the municipal victims were communities with fewer than 50K residents.
With that in mind, Cybernews has created a free tool that monitors ransomware groups’ extortion sites and delivers consolidated feeds of their claims worldwide. This tool provides real-time updates and actionable insights, offers various statistical insights into data, and the ability to determine attack perpetrators.
Here you 8 tips on how to protect yourself from social engineering
- Think before you act: Attackers create a sense of urgency because they want their victims to recklessly make snap decisions. You should always stop and verify. If your friend or colleague is suddenly asking you for money or to change your password, call them on the phone and ask if they really sent the message.
- Use a strong password and store it correctly: Strong passwords consist of a combination of uppercase and lowercase letters, numbers, and special symbols such as punctuation. They should be at least 12 characters long, although we recommend making them even lengthier. Also, employees shouldn’t use passwords that are based on their personal information and contain memorable keyboard paths.
- Check the message for legitimacy: If you’ve received an email and something about it seems off, it probably is. Verify domain names – they could end in .co or .con rather than .com, for example. Typos and other spelling errors can be a clear giveaway that it’s an attempt at a phishing scam.
- Don’t trust senders you don’t know: If you’re not expecting anything, don’t open any files you’ve received. Especially if they are marked with urgent flares.
- If you’re unsure if some website is genuine or a phishing attempt, look for CA certificates, especially if you’re connecting to banking sites.
- Ensure that your systems are up to date with the latest security patches and software updates. Employ robust antivirus and anti-malware solutions, along with intrusion detection systems, to identify and block potential threats. Software vendors frequently release updates to patch bugs. If employees don’t install those updates they may be using vulnerable versions of software.
- Use 2FA authentication for better protection.
- Regularly conduct cybersecurity training and simulated phishing exercises to raise awareness and reinforce good security habits. By adopting a proactive and vigilant approach, providing employees with information about the subject can help them recognize social engineering attacks immediately and mitigate the impact of a coordinated attack.
About the Author: Cybernews Team
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ransomware)