Prevent ransomware attacks with email security
Cyber crime is becoming increasingly sophisticated and broader in scope. In this guide we explain what the most dangerous cyber security threats to businesses are and how to guard against them by putting a robust email security strategy in place to protect your organization.
Contents
The biggest cyber security threats to business in 2023
Cyber Security Hub’s latest survey on the state of cyber security in North America, Europe and the Middle East, found that 40 percent of respondents said that the volume of cyber attacks against their company had increased in the past 12 months.
Malware and ransomware were identified as the biggest threats, followed by key employee targeting and malicious or unsafe mobile apps.
Experts believe that this threat is set to increase. Chief security officer at technology media company MediaPeanut, Camila Serrano, says that geopolitical factors are playing a bigger role in attacks on critical infrastructure, with ransomware attacks becoming more disruptive and malicious actors demanding larger ransoms and causing significant operational issues.
Those carrying out attacks search for the smallest of openings to break into an organizations’ infrastructure to facilitate enormous financial rewards.
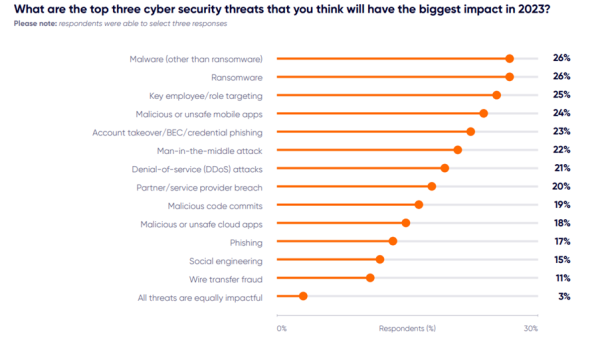
Source: Mid-year state of cyber security report: EMEA and NAM
Once malware threat actors have used phishing emails to infect organizations’ machines and networks, these attacks spread laterally, with access sold to ransomware brokers. Ransomware groups are conscious of the fact that large corporations are more likely to pay multimillion dollar ransoms, but national governments cannot rest on their laurels either; in 2021, Cyber Research Labs documented 48 government agencies spanning 21 countries that were affected by ransomware.
Threat actors’ tactics are becoming ever more sinister. When combined with the migration to cloud email access – which comes with its own security implications – it is more important than ever to detect and block malicious actors from compromising businesses’ data and information via email attacks.
How ransomware gangs target emails
As the ransomware-as-a-service (RaaS) economy matures, ransomware gangs are demonstrating supreme confidence in their debilitating actions.
Recently, Costa Rica’s government was held hostage by the Conti Group, which demanded a US$20m ransom and threatened to overthrow the government if their demands were not met. Other types of attacks using email as a vector include business email compromise (BEC), spam and botnets.
According to a US Federal Bureau of Investigation (FBI) report from May 2022, BEC scams represented a $43bn loss across both international and domestic US organizations between June 2016 and December 2022. During that timeframe the FBI was alerted to more than 240,000 BEC incidents.
“Hackers may pose as job seekers in the hope that HR personnel will open emails and attachments from unknown senders.”
In terms of the data that is targeted, during the early phase of an attack it may be low-level data. Ultimately, however, groups are looking to steal more sensitive data which influences who they are targeting.
One example lies with human resources (HR), as hackers may pose as job seekers in the hope that HR personnel will open emails and attachments from unknown senders, allowing the ransomware to spread. Attackers then have access to confidential and sensitive company information.
While it is important to implement security measures that are offered by email providers, for example, there are additional tactics you should consider beyond the traditional security stack.
Creating a strategy to prevent ransomware attacks
To overcome changing defensive tactics, attackers will always look for new avenues to exhibit their criminal abilities. One such method, telephone-oriented attack delivery (TOAD), does not have a payload – instead it uses a phone number that when called, is answered by a bad actor who directs the victim to manually download malicious content, infecting their computer with ransomware.
As the challenges change, organizations need to treat the playing field as if it will never be fair to them. By adding layers to their security strategies, however, they stand a good chance of deterring ransomware gangs.
Unfortunately email compromises are growing exponentially due to ever more sophisticated methods and automation that goes beyond scanning, blocking and identifying bad actors sending messages.
“Everyone within a company, from interns to the CEO, are prime targets for threat actors seeking access to deploy ransomware.”
Solutions include adding layers such as Domain-based Message Authentication, Reporting, and Conformance (DMARC) email authentication to have a better chance of stopping email fraud or BEC in its tracks. Also, implementing isolation training for at-risk users that aligns with their email risk, or isolation of URLs clicked on from email. Other methods include mSOAR – the automatic remediation of malicious messages post-delivery; abuse mailbox automation; and enhanced data protection such as email DLP and encryption.
Everyone within a company, from interns to the CEO, are prime targets for threat actors seeking access to deploy ransomware. Even gaining access to a small foothold in a business using a compromised employee account can have devastating consequences. Malicious actors can move laterally, escalating the privileges they have access to until they have the ability to take over a company’s entire enterprise network.
Best practices for email security
A comprehensive email security strategy can easily be implemented. Here are some tips:
- Use strong passwords and email encryption. This should be used for both email content and attachments. Security best practices for bring your own device (BYOD) should also be employed by companies that allow their staff access to corporate email on personal devices.
- Use malware sandbox analysis inline. Employees should not forward emails until they have been checked. Companies should also implement software to scan incoming communications and block those that contain malicious software.
- Get a cloud access security broker (CASB) solution. When an email account is compromised it has the potential to cause a huge amount of damage in potential data loss or attacks launched from a compromised email account to other internal or third-party users. A CASB solution can help identify and remediate potentially suspicious logins.
- Implement a data protection solution to identify sensitive data and prevent it from being lost via email. This is because malware developers are leasing out their skills to affiliates who use turn-key solutions to infect victims. In turn, it is becoming easier and more profitable for less-skilled criminals to seize enterprise networks with military-grade encryption and demand millions for the key to the files.
- Partner with identity access management vendors. These can automatically reset passwords in cases where credentials have been potentially compromised. Experts recommend enforcing stricter authentication for users who receive targeted attacks.
- Backup important data securely. Threat actors may attempt to poison or delete backups during their operations. With multi-layered intrusions being the new normal, organizations should always assume all systems are important enough to be patched, protected and monitored.
Empowering employees to prevent ransomware attacks
Organizations need to achieve stronger visibility of the ransomware threats they face, but also ensure their workforces are alert to the risks they are exposed to through education, support and network protections.
By understanding ransomware risk, organizations will be able to effectively shift their approach and prevent an attack from happening.
The solutions exist and selecting the right partners helps organizations maintain their focus on their own goals and aims.
Most threat actors are motivated by financial reward, so protecting data and ensuring staff are educated should never be up for debate. Organizations should focus on behavior rather than artifacts to have a stronger defence against ever-evolving threats.
Finally, a people-centric approach to ransomware may not be typical, but it is necessary given the risks. While endpoints and other technology can help stop ransomware after activated, it is always easier to stop attacks before they start.
- This article was originally published on January 30th, 2023 and updated on August 4th, 2023.

