Phobos Ransomware Aggressively Targeting U.S. Critical Infrastructure
U.S. cybersecurity and intelligence agencies have warned of Phobos ransomware attacks targeting government and critical infrastructure entities, outlining the various tactics and techniques the threat actors have adopted to deploy the file-encrypting malware.
“Structured as a ransomware as a service (RaaS) model, Phobos ransomware actors have targeted entities including municipal and county governments, emergency services, education, public healthcare, and critical infrastructure to successfully ransom several million in U.S. dollars,” the government said.
The advisory comes from the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Multi-State Information Sharing and Analysis Center (MS-ISAC).
Active since May 2019, multiple variants of Phobos ransomware have been identified to date, namely Eking, Eight, Elbie, Devos, Faust, and Backmydata. Late last year, Cisco Talos revealed that the threat actors behind the 8Base ransomware are leveraging a Phobos ransomware variant to conduct their financially motivated attacks.
There is evidence to suggest that Phobos is likely closely managed by a central authority, which controls the ransomware’s private decryption key.
Attack chains involving the ransomware strain have typically leveraged phishing as an initial access vector to drop stealthy payloads like SmokeLoader. Alternatively, vulnerable networks are breached by hunting for exposed RDP services and exploiting them by means of a brute-force attack.
A successful digital break-in is followed by the threat actors dropping additional remote access tools, taking advantage of process injection techniques to execute malicious code and evade detection, and making Windows Registry modifications to maintain persistence within compromised environments.
“Additionally, Phobos actors have been observed using built-in Windows API functions to steal tokens, bypass access controls, and create new processes to escalate privileges by leveraging the SeDebugPrivilege process,” the agencies said. “Phobos actors attempt to authenticate using cached password hashes on victim machines until they reach domain administrator access.”
The e-crime group is also known to use open-source tools such as Bloodhound and Sharphound to enumerate the active directory. File exfiltration is accomplished via WinSCP and Mega.io, after which volume shadow copies are deleted in an attempt to make recovery harder.
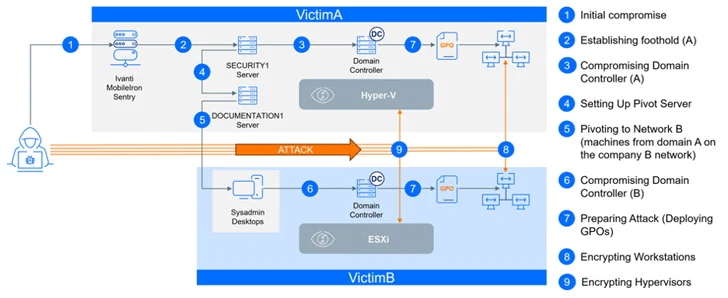
The disclosure comes as Bitdefender detailed a meticulously coordinated ransomware attack impacting two separate companies at the same time. The attack, described as synchronized and multifaceted, has been attributed to a ransomware actor called CACTUS.
“CACTUS continued infiltrating the network of one organization, implanting various types of remote access tools and tunnels across different servers,” Martin Zugec, technical solutions director at Bitdefender, said in a report published last week.
“When they identified an opportunity to move to another company, they momentarily paused their operation to infiltrate the other network. Both companies are part of the same group, but operate independently, maintaining separate networks and domains without any established trust relationship.”
The attack is also notable for the targeting of the unnamed company’s virtualization infrastructure, indicating that CACTUS actors have broadened their focus beyond Windows hosts to strike Hyper-V and VMware ESXi hosts.
It also leveraged a critical security flaw (CVE-2023-38035, CVSS score: 9.8) in an internet-exposed Ivanti Sentry server less than 24 hours after its initial disclosure in August 2023, once again highlighting opportunistic and rapid weaponization of newly published vulnerabilities.
Ransomware continues to be a major money spinner for financially motivated threat actors, with initial ransomware demands reaching a median of $600,000 in 2023, a 20% jump from the previous year, according to Arctic Wolf. As of Q4 2023, the average ransom payment stands at $568,705 per victim.
What’s more, paying a ransom demand does not amount to future protection. There is no guarantee that a victim’s data and systems will be safely recovered and that the attackers won’t sell the stolen data on underground forums or attack them again.
Data shared by cybersecurity company Cybereason shows that “a staggering 78% [of organizations] were attacked again after paying the ransom – 82% of them within a year,” in some cases by the same threat actor. Of these victims, 63% were “asked to pay more the second time.”