Major Phishing-as-a-Service Syndicate ‘BulletProofLink’ Dismantled by Malaysian Authorities
Malaysian law enforcement authorities have announced the takedown of a phishing-as-a-service (PhaaS) operation called BulletProofLink.
The Royal Malaysia Police said the effort, which was carried out with assistance from the Australian Federal Police (AFP) and the U.S. Federal Bureau of Investigation (FBI) on November 6, 2023, was based on information that the threat actors behind the platform were based out of the country.
To that end, eight individuals aged between 29 and 56, including the syndicate’s mastermind, have been arrested across different locations in Sabah, Selangor, Perak, and Kuala Lumpur, New Straits Times reported.
Along with the arrests, authorities confiscated servers, computers, jewelry, vehicles, and cryptocurrency wallets containing approximately $213,000.
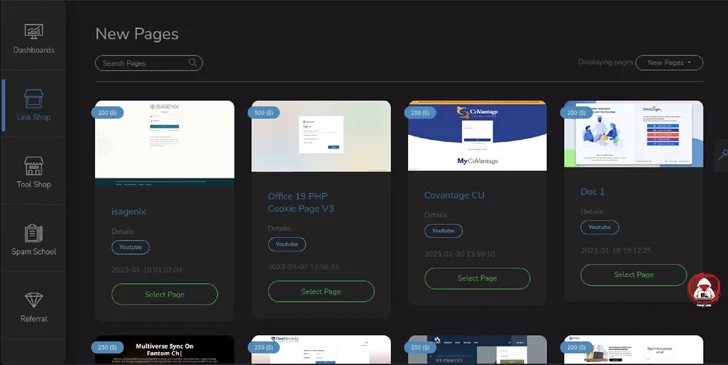
BulletProofLink, also called BulletProftLink, is known for offering ready-to-use phishing templates on a subscription basis to other actors for conducting credential harvesting campaigns. These templates mimic the login pages of well-known services like American Express, Bank of America, DHL, Microsoft, and Naver.
According to an analysis from Microsoft in September 2021, BulletProofLink actors also engaged in what’s called double theft wherein the stolen credentials are sent to both their customers and the core developers, resulting in additional monetization avenues.
“BulletProftLink is associated with the threat actor AnthraxBP who also went by the online nicknames TheGreenMY and AnthraxLinkers,” cybersecurity firm Intel 471 said last week.
“The actor maintained an active website advertising phishing services. The actor has an extensive underground footprint and operated on a number of clear web underground forums and Telegram channels using multiple handles.”
Believed to be active since at least 2015, BulletProftLink’s online storefront is estimated to have no less than 8,138 active clients and 327 phishing pages templates as of April 2023.
Another noteworthy feature is its integration of the Evilginx2 to facilitate adversary-in-the-middle (AiTM) attacks that make it possible for threat actors to steal session cookies and bypass multi-factor authentication protections.
“PhaaS schemes like BulletProftLink provide the fuel for further attacks,” Intel 471 said. “Stolen login credentials are one of the primary ways that malicious hackers gain access to organizations.”
In a sign that threat actors are constantly updating tactics in response to disruptions and taking more sophisticated approaches, AiTM attacks have also been observed employing intermediary links to documents hosted on file-sharing solutions like DRACOON that contain the URLs to adversary-controlled infrastructure.
“This new method can bypass email security mitigations since the initial link appears to be from a legitimate source and no files are delivered to the victim’s endpoint as the hosted document containing the link can be interacted with via the file-sharing server within the browser,” Trend Micro said.
The development comes as a 33-year-old Serbian and Croatian national, Milomir Desnica, pleaded guilty in the U.S. to operating a drug trafficking platform called Monopoly Market on the dark web and for conspiring to distribute over 30 kilograms of methamphetamine to U.S. customers.
The illicit marketplace, which was set up by Desnica in 2019, was taken offline in December 2021 as part of a coordinated exercise in partnership with Germany and Finland. Desnica was arrested in Austria in November 2022 and extradited to the U.S. to face drug trafficking charges in June 2023.