DDoS 2.0: IoT Sparks New DDoS Alert
The Internet of Things (IoT) is transforming efficiency in various sectors like healthcare and logistics but has also introduced new security risks, particularly IoT-driven DDoS attacks. This article explores how these attacks work, why they’re uniquely problematic, and how to mitigate them.
What Is IoT?
IoT (Internet of Things) refers to online, interconnected devices that collect and exchange data. This broad category of devices includes sensors, cameras, network routers, and advanced machinery, and their integration into everyday life and work processes results in an ecosystem that can automate operations, improve decision-making, and enhance user experience.
IoT: A Breeding Ground for Botnets
IoT’s rapid adoption amplifies its vulnerability, as poorly secured devices become easy prey for attackers and may become part of a botnet. Controlled by attackers, botnets can scale and rapidly execute various attacks, including DDoS, data theft, ad fraud, cryptocurrency mining, spam and phishing, data harvesting, and snooping—without device owners’ knowledge.
Why are IoT Botnets a Growing Concern?
Botnets are nothing new, but IoT botnets pose a specific threat. The number of IoT devices reached 16 billion in 2022 and is expected to exceed 30 billion by 2025. These devices often suffer from infrequent updates or insecure default settings, or are simply left unattended, making them less secure than traditional computers and are at risk of being hijacked with relative ease to form potent botnets.
The scale and complexity of IoT-driven attacks are set to rise due to their increasing use. Among these risks, distributed denial-of-service (DDoS) attacks stand out as particularly challenging to mitigate. The distributed nature of IoT devices renders them ideal platforms for these attacks, making it difficult to identify and block malicious traffic and thereby compounding the challenges of DDoS mitigation.
Anatomy of IoT-Driven botnet DDoS Attacks
Let’s discuss how IoT DDoS attacks happen and how new IoT devices join the ranks of bots.
How Are IoT DDoS Attacks Launched?
There are several key entities involved in a DDoS botnet attack:
- The attacker is the person who controls the botnet. They are also known as the bot herder or botmaster.
- A command-and-control (C&C) server is a computer controlled by the attacker and used to communicate with the infected devices. The C&C orchestrates the botnet’s actions, sending out global commands for tasks like initiating an attack or scanning a new device for vulnerabilities.
- A botnet is a network of devices that have been infected with malware and are controlled by a single attacker.
- The victim or target is the focus of a specific botnet-driven attack.
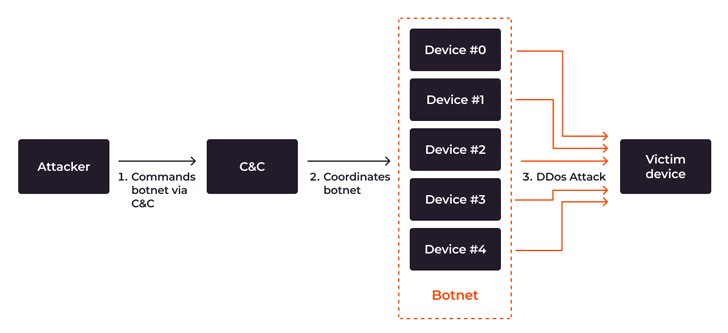 |
| DDoS botnet assault flow from attacker’s command to DDoS attack |
The attack process is relatively straightforward:
- The attacker targets the botnet to a victim. The botnet operator identifies the target—usually a device, website, or online service—that they want to take down.
- The C&C server orchestrates the DDoS attack. The C&C server sends the attacker’s instructions to all the bots in the network to start sending requests to the target, and coordinates the botnet’s behavior.
- A flood of traffic occurs. All the bots in the network start sending a large number of requests to the target website or server.
When the botnet floods the target with excessive requests, service failures occur which jeopardize the availability of the targeted system and even put the integrity of the whole infrastructure at risk. When aimed against essential infrastructures such as healthcare or transportation, the hazards go beyond financial and reputational harm to endangering people’s lives.
Incorporating IoT Devices into Botnets
IoT devices that are unpatched, unattended, or misconfigured, or are already under botnet DDoS attack, are at risk of being incorporated into a botnet. To expand the botnet, an attacker hacks new IoT devices. This process involves two entities: the botnet itself and the loader server, a special server that infects other devices.
In brief, the process goes like this: The botnet hacks the device and gains access, and then the loader server installs malware on it. The attacker then gains permanent access to the device and attaches it to the botnet. Here are the stages of infecting IoT devices and connecting them to a botnet based the Mirai case:
- Initial command: The attacker uses the C&C server to send a command to the botnet for attacking and incorporating new devices.
- Orchestration: The C&C server coordinates the botnet’s actions.
- Scanning and compromise: The botnet scans and compromises victim devices to gain privileged access by brute-forcing weak passwords or exploiting outdated firmware or insecure configurations.
- Data reporting: The botnet relays the victim’s IP address and access credentials to the loader server once the device is hacked.
- Malware delivery and infection: The loader server sends malware or malicious instructions, which are then executed by a compromised device, turning it into a bot.
- Joining the botnet: The newly infected device becomes part of the botnet and awaits further commands, often operating undetected.
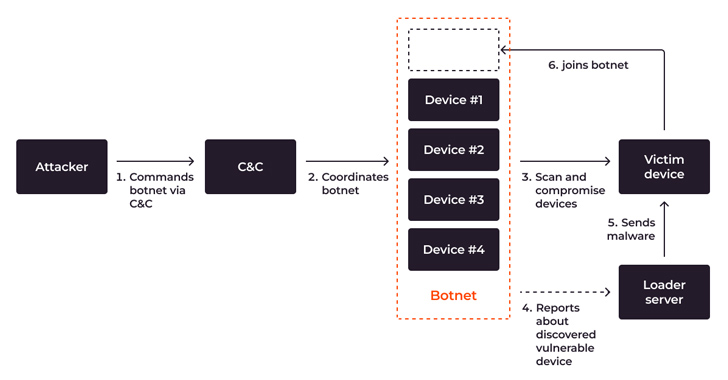 |
| Process flow, demonstrating scanning, compromising, infecting and joining a new device to a botnet |
Advanced botnets can self-propagate, compromising more devices autonomously, bringing more and more devices into the botnet, expanding the botnet’s size and amplifying the scale of future attacks.
How Dangerous Is the Current IoT DDoS Threat?
IoT-driven DDoS attacks increased by 300% in the first half of 2023 alone, causing an estimated global financial loss of $2.5 billion. In 2023, 90% of complex, multi-vector DDoS attacks were based on botnets. The trend shows no signs of slowing down: the number of IoT devices engaged in botnet-driven DDoS attacks rose from around 200,000 a year ago to approximately 1 million devices, while there are twice as many vulnerabilities being targeted by botnet malware.
Overall, DDoS attack capacity is on the rise. According to Gcore’s Radar 2023, the top power of a singular DDoS attack reached a staggering 800 Gbps in the first half of 2023. Just two years earlier, it peaked at 300 Gbps. While most attacks hit 1–2 Tbps speeds, the most potent can reach 100 Tbps.
Alarming Projections for 2023–2024
We are witnessing a significant increase in specific DDoS attack vectors, such as UDP reflection and HTTP request flooding, primarily targeting the technology and financial industries. Sectors heavily reliant on online services and real-time data processing are the most attractive targets, facing immediate financial losses and long-term reputational damage.
IoT’s advancement, while driving innovation, also brings alarming future trends in cybersecurity: it fuels innovation but also raises significant cybersecurity concerns. With an expected 18% growth in IoT devices to 14.4 billion in 2023, and a projected increase to 27 billion by 2025, experts anticipate a corresponding surge in botnet attacks. With both IoT and DDoS on the rise, IoT DDoS are posed to become an increasingly substantial threat in the immediate future.
Defensive Measures: Strategies and Best Practices
The rise of more sophisticated and powerful attacks makes immediate attention to security essential. Here’s how various stakeholders can contribute to a more secure digital ecosystem:
1. Protect your IoT from being infected.
- Educate on safe IoT practices: Encourage home and corporate users to change default passwords, update firmware, and adhere to best practices to prevent devices from being compromised. Many companies, like SANS Institute, offer training on IoT security and penetration testing.
- Collaborate and threat share: Initiatives like the Cyber Threat Alliance and the Joint Cyber Defense Collaborative unite governments, tech companies, and cybersecurity firms to rapidly detect and neutralize emerging threats, strengthening collective global defenses.
- Regularly update devices: Ensure IoT devices are updated with the latest firmware and patches to prevent known vulnerabilities from being exploited.
2. Protect against IoT-driven botnet DDoS attacks.
- Implement multi-layer security protocols: Deploy a comprehensive security strategy, from firewalls and intrusion detection systems to web application security solutions.
- Invest in Specialized DDoS Protection Solutions: Companies like Gcore have developed solutions explicitly designed to combat even massive, IoT-driven DDoS attacks. These DDoS protection solutions have been pivotal in reducing risks by leveraging real-time analytics.
Conclusion
The challenge of defending against IoT-driven DDoS attacks is an ongoing battle. By understanding current solutions, investing in specialized technologies like Gcore’s DDoS protection, and fostering a culture of vigilance and collaboration, you can significantly reduce organizational risks and help pave the way for a more secure digital landscape in the face of escalating threats.