Cyber Group ‘Gold Melody’ Selling Compromised Access to Ransomware Attackers
A financially motivated threat actor has been outed as an initial access broker (IAB) that sells access to compromised organizations for other adversaries to conduct follow-on attacks such as ransomware.
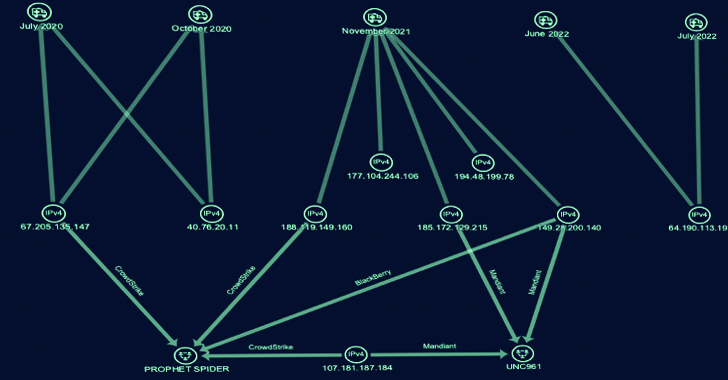
SecureWorks Counter Threat Unit (CTU) has dubbed the e-crime group Gold Melody, which is also known by the names Prophet Spider (CrowdStrike) and UNC961 (Mandiant).
“This financially motivated group has been active since at least 2017, compromising organizations by exploiting vulnerabilities in unpatched internet-facing servers,” the cybersecurity company said.
“The victimology suggests opportunistic attacks for financial gain rather than a targeted campaign conducted by a state-sponsored threat group for espionage, destruction, or disruption.”

Gold Melody has been previously linked to attacks exploiting security flaws in JBoss Messaging (CVE-2017-7504), Citrix ADC (CVE-2019-19781), Oracle WebLogic (CVE-2020-14750 and CVE-2020-14882), GitLab (CVE-2021-22205), Citrix ShareFile Storage Zones Controller (CVE-2021-22941), Atlassian Confluence (CVE-2021-26084), ForgeRock AM (CVE-2021-35464), and Apache Log4j (CVE-2021-44228) servers.
The cybercrime group has been observed expanding its victimology footprint to strike retail, health care, energy, financial transactions, and high-tech organizations in North America, Northern Europe, and Western Asia as of mid-2020.
Mandiant, in an analysis published in March 2023, said that “in multiple instances, UNC961 intrusion activity has preceded the deployment of Maze and Egregor ransomware from distinct follow-on actors.”
It further described the group as “resourceful in their opportunistic angle to initial access operations” and noted it “employs a cost-effective approach to achieve initial access by exploiting recently disclosed vulnerabilities using publicly available exploit code.”
Besides relying on a diverse arsenal comprising web shells, built-in operating system software, and publicly available utilities, it’s known to employ proprietary remote access trojans (RATs) and tunneling tools such as GOTROJ (aka MUTEPUT), BARNWORK, HOLEDOOR, DARKDOOR, AUDITUNNEL, HOLEPUNCH, LIGHTBUNNY, and HOLERUN to execute arbitrary commands, gather system information, and establish a reverse tunnel with a hard-coded IP address.
Secureworks, which linked Gold Melody to five intrusions between July 2020 and July 2022, said these attacks entailed the abuse of a different set of flaws, including those impacting Oracle E-Business Suite (CVE-2016-0545), Apache Struts (CVE-2017-5638), Sitecore XP (CVE-2021-42237), and Flexera FlexNet (CVE-2021-4104) to obtain initial access.
Level-Up SaaS Security: A Comprehensive Guide to ITDR and SSPM
Stay ahead with actionable insights on how ITDR identifies and mitigates threats. Learn about the indispensable role of SSPM in ensuring your identity remains unbreachable.
A successful foothold is succeeded by the deployment of web shells for persistence, followed by creating directories in the compromised host to stage the tools used in the infection chain.
“Gold Melody conducts a considerable amount of scanning to understand a victim’s environment,” the company said. “Scanning begins shortly after gaining access but is repeated and continued throughout the intrusion.”
The reconnaissance phase paves the way for credential harvesting, lateral movement, and data exfiltration. That said, all five attacks ultimately proved to be unsuccessful.
“Gold Melody acts as a financially motivated IAB, selling access to other threat actors,” the company concluded. “The buyers subsequently monetize the access, likely through extortion via ransomware deployment.”
“Its reliance on exploiting vulnerabilities in unpatched internet-facing servers for access reinforces the importance of robust patch management.”