Stealing Credentials Through Legitimate Dropbox Pages
Today, we’re writing about cyberattacks that occur via Dropbox.
Dropbox, the popular file-sharing service, is used around the globe. Cybercriminals have figured out that they can use it to create documents that host phishing material.
In the first two weeks of September, we saw 5,440 of these attacks.
Here’s how it works. Someone creates a free Dropbox account. Then they create a document and share it with a colleague or friend. The recipient receives a notification directly from Dropbox, saying that someone has shared content that is awaiting comment or reply via a click. The email comes directly from Dropbox and is legitimate. The recipient’s email security service would not—and should not—block that, because it is legitimately from Dropbox. When the link in the email is clicked, it directs to a Dropbox page. That page is also legitimate—it’s a Dropbox page. There’s no spoofing. Embedded within that page, however, is a link that redirects the recipient to an external page that’s designed to steal their credentials.
This represents the continued shift by hackers. No longer do hackers have to spoof legitimate sites. In fact, all they had to do was sign up for a free account at a legitimate site like Dropbox. No coding experience necessary. There’s no brand impersonation here. It’s the actual brand.
Dropbox is not being hacked or exploited here. Rather, hackers are creating free Dropbox accounts and then putting malicious content onto that page. The recipient’s email security service won’t block it, and end-users won’t think it’s suspicious. Because it’s not! And when they click on the link, that also goes to a safe Dropbox page. It’s only when they click on the link embedded in the Dropbox page is the danger apparent. And then it’s too late.
This is a novel method by hackers that we call BEC 3.0. It’s the third evolution of Business Email Compromise attacks. Instead of spoofing CEOs or partners, now hackers are able to send emails directly from legitimate services, saving time, money and hassle, and able to spray these out at scale.
These attacks are increasing, and hackers are using all your favorite productivity sites—Google, Dropbox, QuickBooks, PayPal and more. It’s one of the cleverer innovations we’ve seen, and given the scale of this attack thus far, it’s one of the most popular and effective.
Attack
In this attack, hackers are utilizing Dropbox documents to host credential-harvesting sites.
- Vector: Email
- Type: BEC 3.0
- Techniques: Social Engineering, Credential Harvesting
- Target: Any end-user
Email Example
This attack starts with an email that comes directly from Dropbox.
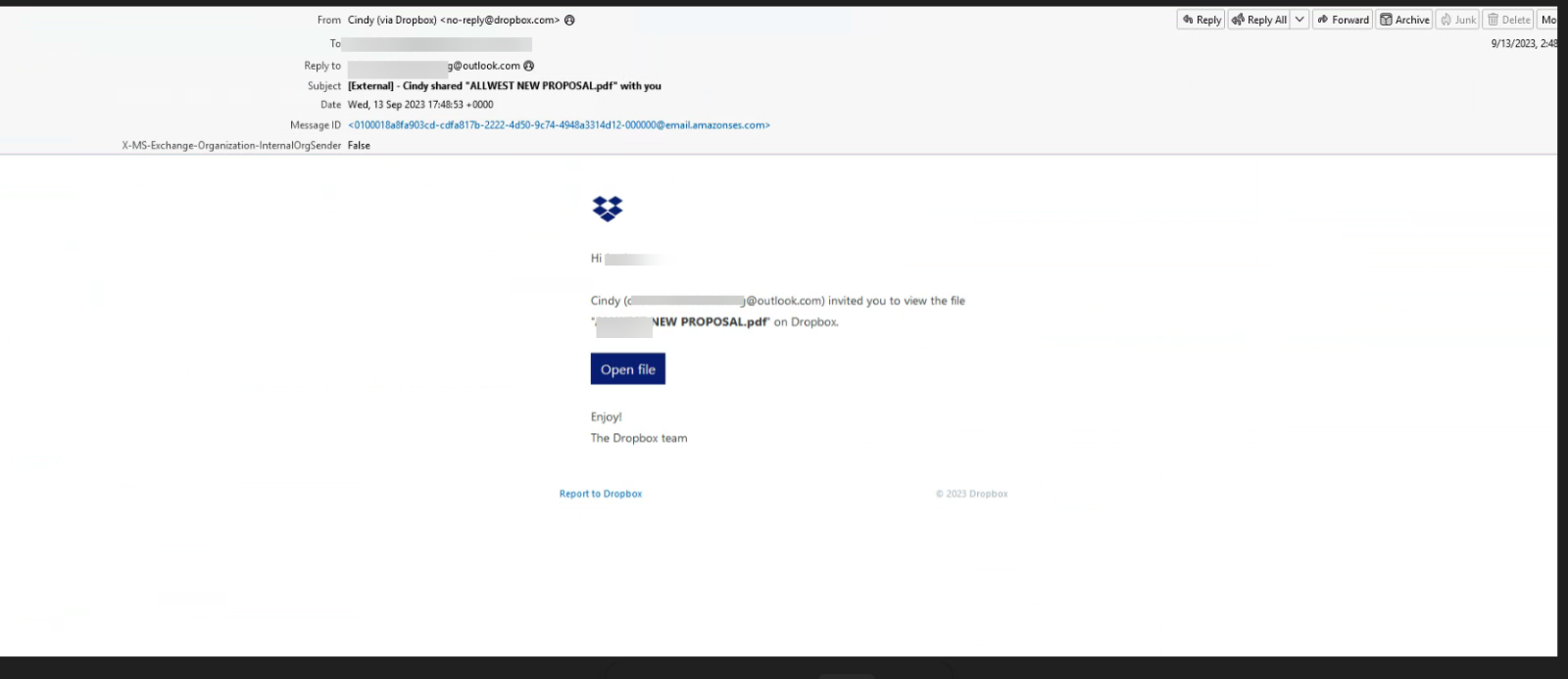
This is a standard email that anyone would receive from Dropbox, notifying them that there’s a document to view.
From there, the user is directed to a legitimate Dropbox page:
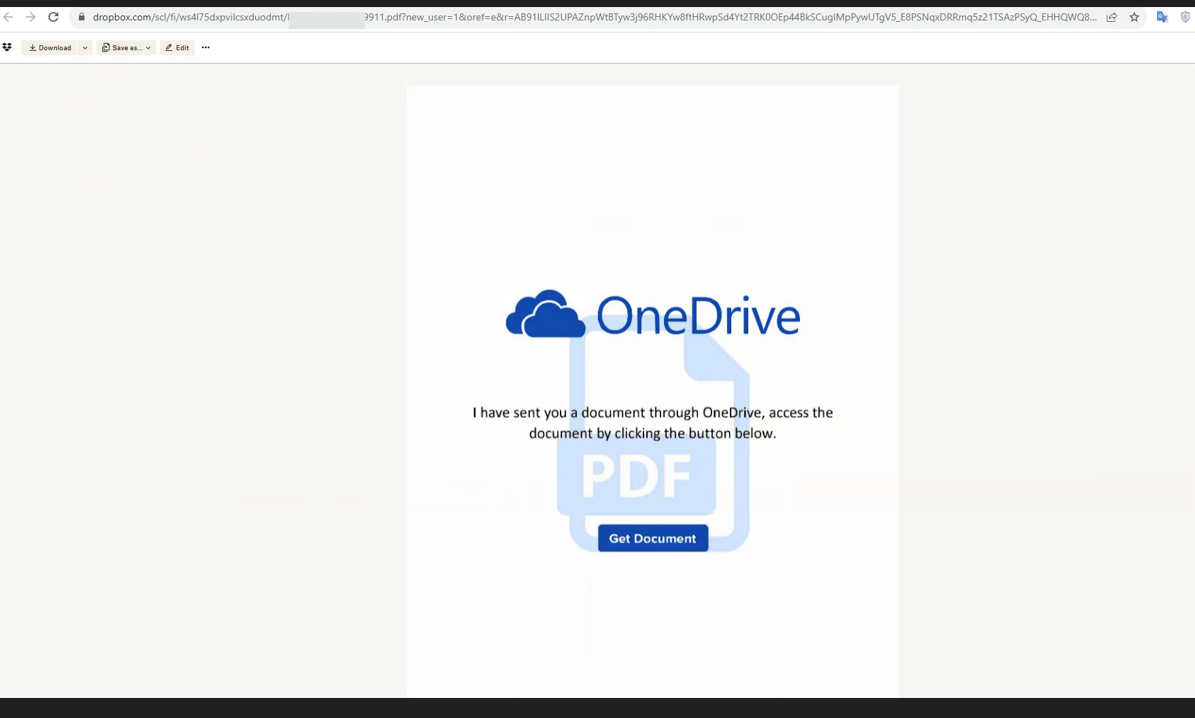
Though the content is that of a OneDrive look-a-like page, the URL is hosted on Dropbox.
When you click on “Get Document”, the user is directed to this final page. This is the credential harvesting page.
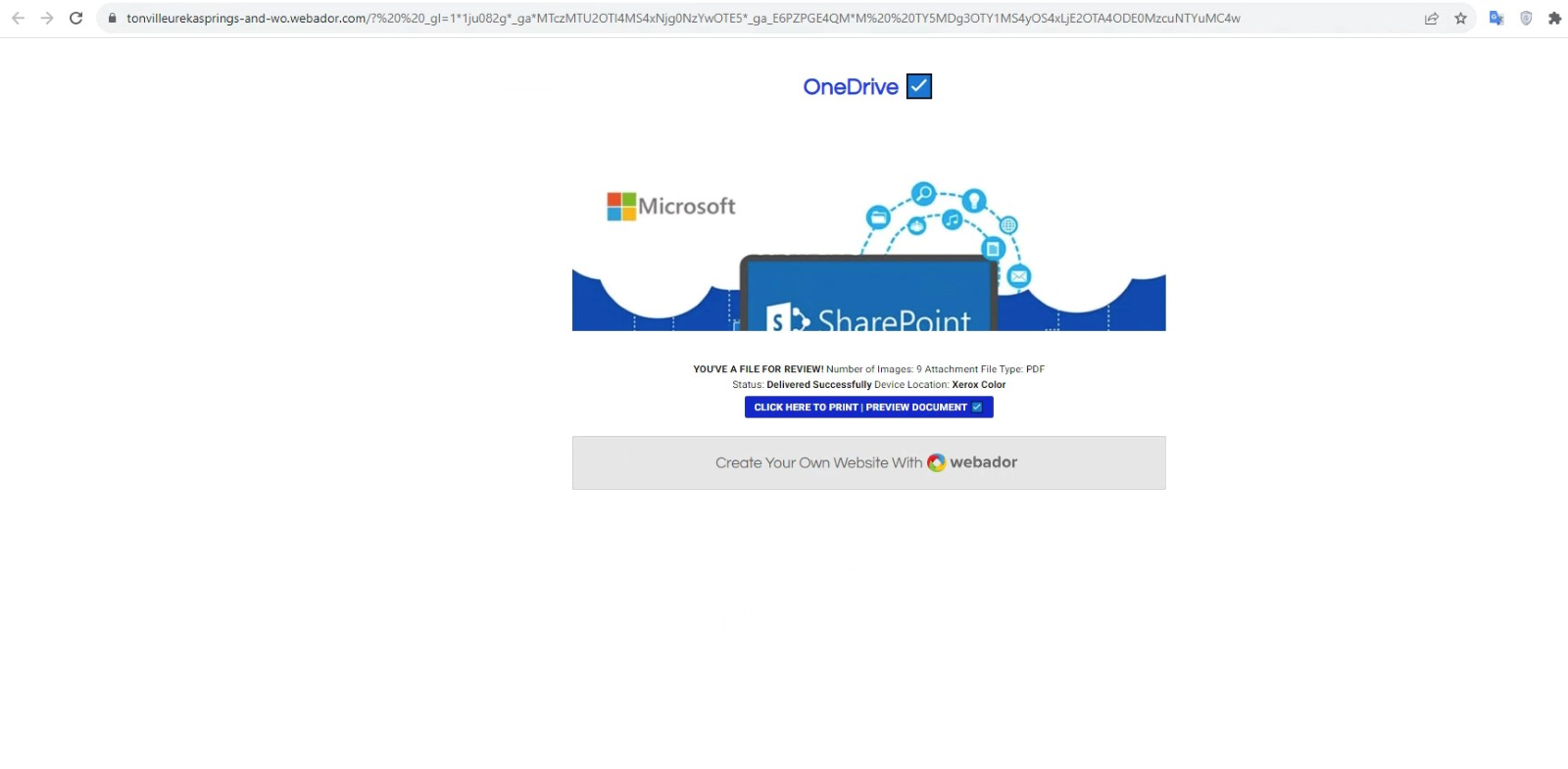
This is the page that is hosted outside of Dropbox, and where the threat actors want you to click in order to steal your credentials.
Techniques
Business Email Compromise has undergone a pretty rapid evolution.
It was only a few years ago that we were writing about so-called “Gift card” scams. These were emails that pretended to come from a CEO or an executive, asking an underling to purchase “gift cards”. The idea is that the hackers would then use the gift cards for personal gain. These emails typically came from spoofed Gmail addresses–think [email protected], not [email protected].
We might also see impersonation of domains and partners, but these were always spoofs, not the real deal.
The next evolution came from compromised accounts. This may be an internal user compromised, such as someone in finance, or even a partner user compromised. These attacks are even trickier because they comes from a legitimate address. But you might see a link to a fake O365 login page, or stilted language that NLP can pick up on.
But now we have BEC 3.0, which are attacks from legitimate services. NLP is useless here—the language comes directly from legitimate services and nothing is awry. URL scanning isn’t going to work either since it’s going to direct the user to a legitimate Dropbox or other site.
These attacks are incredibly difficult to stop and identify, for both security services and end-users.
Starting with education is critical. End users need to ask themselves—do I know this person sending me a document? And even if you do click on the document, the next thing to ask: does a OneDrive page on a Dropbox document make sense?
Asking those questions can help. As can hovering over the URL on the Dropbox page itself.
But that’s asking a lot of the user.
That’s why these attacks are increasing in frequency and intensity.
Check Point researchers reached out to Dropbox to inform them of this campaign on September 18th.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Adopt AI-powered technology capable of analyzing and identifying numerous phishing indicators to proactively thwart complex attacks.
- Embrace a comprehensive security solution that includes document and file-scanning capabilities
- Deploy a robust URL protection system that conducts thorough scans and emulates webpages for enhanced security
Check Point Customers remain protected against the threats described in this blog while using Harmony Cloud Email & Collaboration Security.
Harmony Email & Collaboration provides complete protection for Microsoft 365, Google Workspace, and all your collaboration and file-sharing apps. Email & Collaboration is designed specifically for cloud email environments and is the ONLY solution that prevents, not just detects or responds to, threats from entering the inbox

