Phishing via Genial.ly
Hackers love to leverage free sites to send phishing campaigns. We’ve seen this a lot over the last year, whether it’s popular sites like Google or PayPal, or lesser-known sites as well. If it’s free, it means there’s no bar to entry and the threat actors can try as often as they like with no downside.
The use of legitimate, free services has been a main theme of the attacks we’ve seen this year. We call it Business Compromise 3.0, the next evolution of the dangerous BEC attacks. These use legitimate sites to carry out illegitimate tasks, and it’s incredibly difficult to stop because the emails themselves are genuine.
In this attack brief, Check Point Harmony Email researchers will discuss how hackers are using Genial.ly to send out phishing links.
Attack
In this attack, hackers are using Genia.ly to send out phishing links.
- Vector: Email
- Type: BEC 3.0
- Techniques: Social Engineering, Credential Harvesting
- Target: Any end-user
Email Example
Genial.ly is a website where anyone can create interactive content. The idea is to turn anything into something more enjoyable to watch and experience.
When someone creates something in Genial.ly, and wants to share it, the recipient gets an email. The email invites the user to click on a link to go to the creation.
In this case, hackers are creating documents in Genial.ly that link to malicious material. Here’s what it looks like:
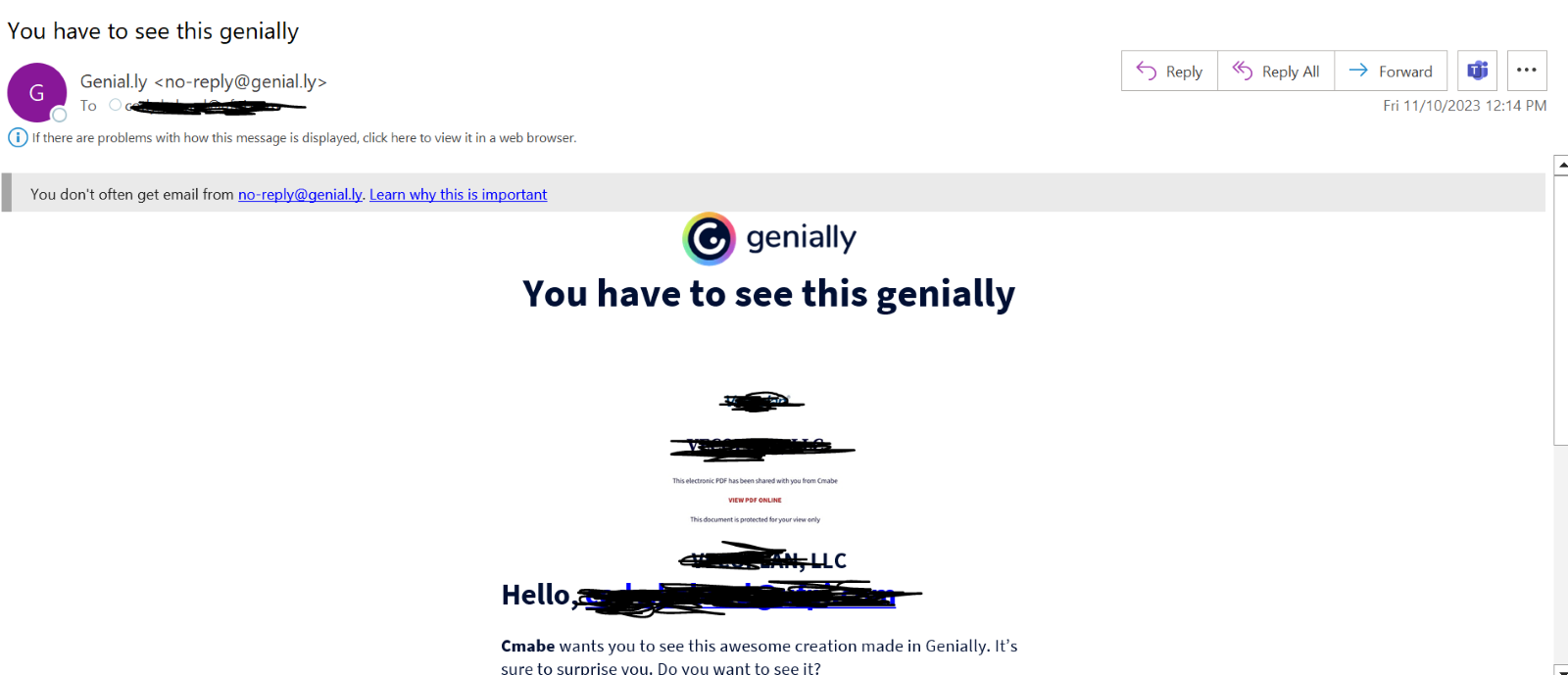
This is a standard email that you would get when someone sends a Genial.ly. And it’s legitimate. It comes directly from the website. The link is a Genial.ly link, re-directing you to the creation.
It’s only when you click on the image in the site that the link takes you to a malicious page.
Techniques
Utilizing legitimate services to send out attacks has been a dominant attack form in 2023, and will likely continue to be in 2024.
Why? It’s easy to deploy, with little to no coding experience required. All you really need is access to a malicious link and some way to receive the information. It’s free. Creating an account doesn’t require a credit card or any other form of payment, and you can create as many accounts as you’d like.
They are very difficult for security solutions to identify. There are no real malicious indicators. It’s a legitimate service. The language in the email is not suspicious.
Without any true protection, your best hope is for users to ignore it, or not click on the link on the first site, in this case Genial.ly. But hoping is not protection.
All hope is not lost, though. Link protection and URL rewriting play a huge role in this. Emulating pages behind links to see the true intent is a must. This covers users even if they click on the malicious link in Genial.ly, because that link can be emulated and it can be determined if it’s malicious or not. Another one is to analyze sites for zero-day phishing indicators or implement a policy that blocks the re-use of corporate passwords and knows when it’s being entered on a site that’s not the corporate email login.
This attack form will continue to ratchet up in 2024, and hackers will find myriad new SaaS sites to use as their springboard.
Harmony Email Researchers informed Genial.ly of this campaign on December 4th.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Implement security that uses AI to look at multiple indicators of phishing
- Implement full-suite security that can scan documents and files
- Implement robust URL protection that scans and emulates webpages

