New Apple Zero-Days Exploited to Target Egyptian ex-MP with Predator Spyware
The three zero-day flaws addressed by Apple on September 21, 2023, were leveraged as part of an iPhone exploit chain in an attempt to deliver a spyware strain called Predator targeting former Egyptian member of parliament Ahmed Eltantawy between May and September 2023.
“The targeting took place after Eltantawy publicly stated his plans to run for President in the 2024 Egyptian elections,” the Citizen Lab said, attributing the attack with high confidence to the Egyptian government owing to it being a known customer of the commercial spying tool.
According to a joint investigation conducted by the Canadian interdisciplinary laboratory and Google’s Threat Analysis Group (TAG), the mercenary surveillance tool is said to have been delivered via links sent on SMS and WhatsApp.
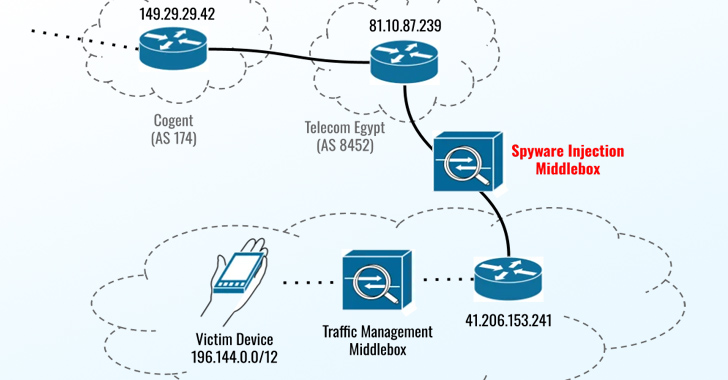
“In August and September 2023, Eltantawy’s Vodafone Egypt mobile connection was persistently selected for targeting via network injection; when Eltantawy visited certain websites not using HTTPS, a device installed at the border of Vodafone Egypt’s network automatically redirected him to a malicious website to infect his phone with Cytrox’s Predator spyware,” the Citizen Lab researchers said.

The exploit chain leveraged a set of three vulnerabilities – CVE-2023-41991, CVE-2023-41992, and CVE-2023-41993 – which could allow a malicious actor to bypass certificate validation, elevate privileges, and achieve remote code execution on targeted devices upon processing a specially crafted web content.
Predator, made by a company called Cytrox, is analogous to NSO Group’s Pegasus, enabling its customers to surveil targets of interest and harvest sensitive data from compromised devices. Part of a consortium of spyware vendors called the Intellexa Alliance, it was blocklisted by the U.S. government in July 2023 for “enabling campaigns of repression and other human rights abuses.”
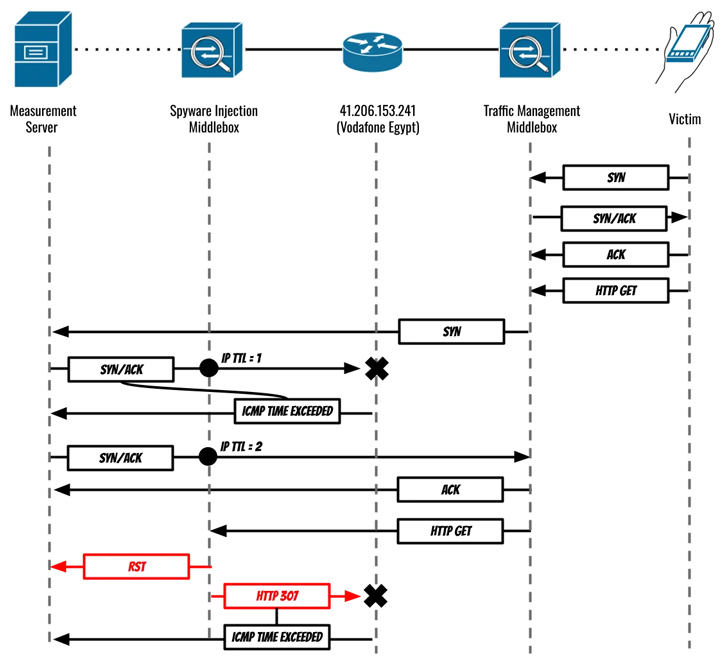
The exploit, hosted on a domain named sec-flare[.]com, is said to have been delivered after Eltantawy was redirected to a website named c.betly[.]me by means of a sophisticated network injection attack using Sandvine’s PacketLogic middlebox situated on a link between Telecom Egypt and Vodafone Egypt.
“The body of the destination website included two iframes, ID ‘if1’ which contained apparently benign bait content (in this case a link to an APK file not containing spyware) and ID ‘if2’ which was an invisible iframe containing a Predator infection link hosted on sec-flare[.]com,” the Citizen Lab said.
Google TAG researcher Maddie Stone characterized it as a case of an adversary-in-the-middle (AitM) attack that takes advantage of a visit to a website using HTTP (as opposed to HTTPS) to intercept and force the victim to visit a different site operated by the threat actor.
“In the case of this campaign, if the target went to any ‘http’ site, the attackers injected traffic to silently redirect them to an Intellexa site, c.betly[.]me,” Stone explained. “If the user was the expected targeted user, the site would then redirect the target to the exploit server, sec-flare[.]com.”
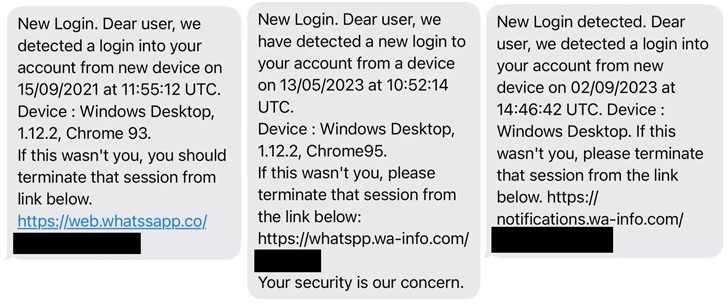
Eltantawy received three SMS messages in September 2021, May 2023, and September 2023 that masqueraded as security alerts from WhatsApp urging Eltantawy to click on a link to terminate a suspicious login session originating from a purported Windows device.
While these links don’t match the fingerprint of the aforementioned domain, the investigation revealed that the Predator spyware was installed on the device approximately 2 minutes and 30 seconds after Eltantawy read the message sent in September 2021.
AI vs. AI: Harnessing AI Defenses Against AI-Powered Risks
Ready to tackle new AI-driven cybersecurity challenges? Join our insightful webinar with Zscaler to address the growing threat of generative AI in cybersecurity.
He also received two WhatsApp messages on June 24, 2023, and July 12, 2023, in which an individual claiming to be working for the International Federation for Human Rights (FIDH) solicited his opinion on an article that pointed to the website sec-flare[.]com. The messages were left unread.
Google TAG said it also detected an exploit chain that weaponized a remote code execution flaw in the Chrome web browser (CVE-2023-4762) to deliver Predator on Android devices using two methods: the AitM injection and via one-time links sent directly to the target.
CVE-2023-4762, a type confusion vulnerability in the V8 engine, was anonymously reported on August 16, 2023, and patched by Google on September 5, 2023, although the internet giant assesses that Cytrox/Intellexa may have used this vulnerability as a zero-day.
According to a brief description on the National Vulnerability Database (NVD), CVE-2023-4762 concerns a “type confusion in V8 in Google Chrome prior to 116.0.5845.179 [that] allowed a remote attacker to execute arbitrary code via a crafted HTML page.”
The latest findings, besides highlighting the abuse of surveillance tools to target the civil society, underscores the blindspots in the telecom ecosystem that could be exploited to intercept network traffic and inject malware into targets’ devices.
“Although great strides have been made in recent years to ‘encrypt the web,’ users still occasionally visit websites without HTTPS, and a single non-HTTPS website visit can result in spyware infection,” the Citizen Lab said.
Users who are at risk of spyware threats because of “who they are or what they do” are recommended to keep their devices up-to-date and enable Lockdown Mode on iPhones, iPads, and Macs to stave off such risks.