Who is Alleged Medibank Hacker Aleksandr Ermakov? – Krebs on Security
Authorities in Australia, the United Kingdom and the United States this week levied financial sanctions against a Russian man accused of stealing data on nearly 10 million customers of the Australian health insurance giant Medibank. 33-year-old Aleksandr Ermakov allegedly stole and leaked the Medibank data while working with one of Russia’s most destructive ransomware groups, but little more is shared about the accused. Here’s a closer look at the activities of Mr. Ermakov’s alleged hacker handles.

Aleksandr Ermakov, 33, of Russia. Image: Australian Department of Foreign Affairs and Trade.
The allegations against Ermakov mark the first time Australia has sanctioned a cybercriminal. The documents released by the Australian government included multiple photos of Mr. Ermakov, and it was clear they wanted to send a message that this was personal.
It’s not hard to see why. The attackers who broke into Medibank in October 2022 stole 9.7 million records on current and former Medibank customers. When the company refused to pay a $10 million ransom demand, the hackers selectively leaked highly sensitive health records, including those tied to abortions, HIV and alcohol abuse.
The U.S. government says Ermakov and the other actors behind the Medibank hack are believed to be linked to the Russia-backed cybercrime gang REvil.
“REvil was among the most notorious cybercrime gangs in the world until July 2021 when they disappeared. REvil is a ransomware-as-a-service (RaaS) operation and generally motivated by financial gain,” a statement from the U.S. Department of the Treasury reads. “REvil ransomware has been deployed on approximately 175,000 computers worldwide, with at least $200 million paid in ransom.”
The sanctions say Ermakov went by multiple aliases on Russian cybercrime forums, including GustaveDore, JimJones, and Blade Runner. A search on the handle GustaveDore at the cyber intelligence platform Intel 471 shows this user created a ransomware affiliate program in November 2021 called Sugar (a.k.a. Encoded01), which focused on targeting single computers and end-users instead of corporations.
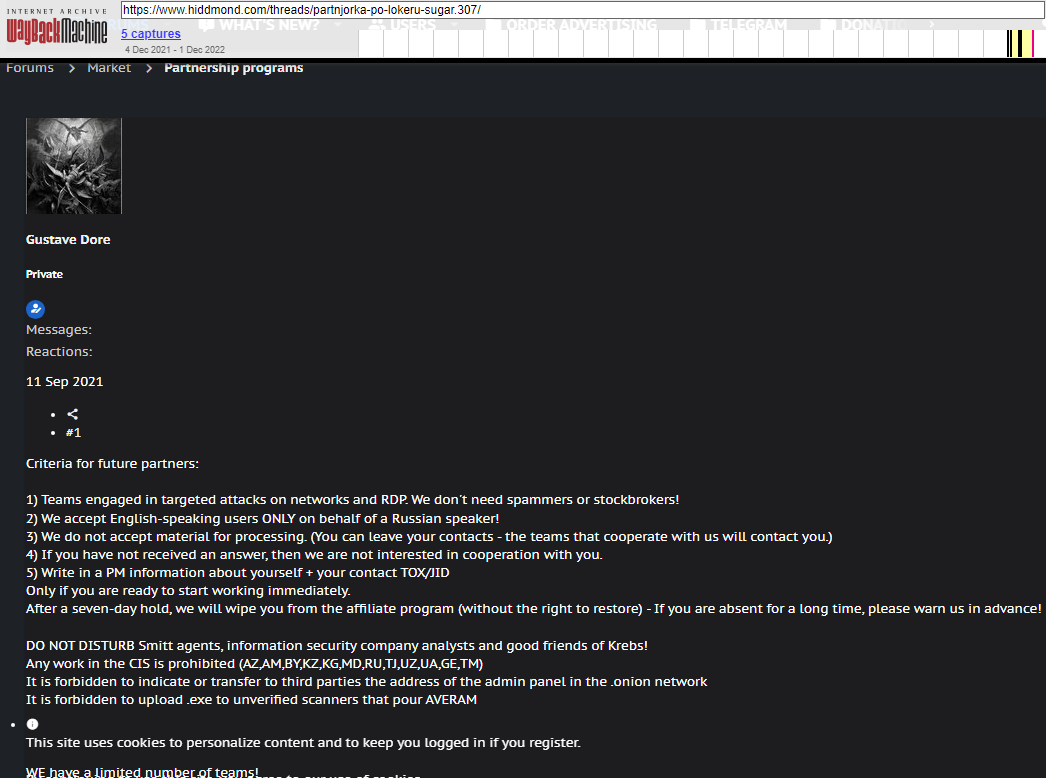
An ad for the ransomware-as-a-service program Sugar posted by GustaveDore warns readers against sharing information with security researchers, law enforcement, or “friends of Krebs.”
In November 2020, Intel 471 analysts concluded that GustaveDore’s alias JimJones “was using and operating several different ransomware strains, including a private undisclosed strain and one developed by the REvil gang.”
In 2020, GustaveDore advertised on several Russian discussion forums that he was part of a Russian technology firm called Shtazi, which could be hired for computer programming, web development, and “reputation management.” Shtazi’s website remains in operation today.
A Google-translated version of Shtazi dot ru. Image: Archive.org.
The third result when one searches for shtazi[.]ru in Google is an Instagram post from a user named Mikhail Borisovich Shefel, who promotes Shtazi’s services as if it were also his business. If this name sounds familiar, it’s because in December 2023 KrebsOnSecurity identified Mr. Shefel as “Rescator,” the cybercriminal identity tied to tens of millions of payment cards that were stolen in 2013 and 2014 from big box retailers Target and Home Depot, among others.
How close was the connection between GustaveDore and Mr. Shefel? The Treasury Department’s sanctions page says Ermakov used the email address [email protected]. A search for this email at DomainTools.com shows it was used to register just one domain name: millioner1[.]com. DomainTools further finds that a phone number tied to Mr. Shefel (79856696666) was used to register two domains: millioner[.]pw, and shtazi[.]net.
The December 2023 story here that outed Mr. Shefel as Rescator noted that Shefel recently changed his last name to “Lenin” and had launched a service called Lenin[.]biz that sells physical USSR-era Ruble notes bearing the image of Vladimir Lenin, the founding father of the Soviet Union. The Instagram account for Mr. Shefel includes images of stacked USSR-era Ruble notes, as well as multiple links to Shtazi.

The Instagram account of Mikhail Borisovich Shefel, aka MikeMike aka Rescator.
Intel 471’s research revealed Ermakov was affiliated in some way with REvil because the stolen Medibank data was published on a blog that had one time been controlled by REvil affiliates who carried out attacks and paid an affiliate fee to the gang.
But by the time of the Medibank hack, the REvil group had mostly scattered after a series of high-profile attacks led to the group being disrupted by law enforcement. In November 2021, Europol announced it arrested seven REvil affiliates who collectively made more than $230 million worth of ransom demands since 2019. At the same time, U.S. authorities unsealed two indictments against a pair of accused REvil cybercriminals.
“The posting of Medibank’s data on that blog, however, indicated a connection with that group, although the connection wasn’t clear at the time,” Intel 471 wrote. “This makes sense in retrospect, as Ermakov’s group had also been a REvil affiliate.”
It is easy to dismiss sanctions like these as ineffective, because as long as Mr. Ermakov remains in Russia he has little to fear of arrest. However, his alleged role as an apparent top member of REvil paints a target on him as someone who likely possesses large sums of cryptocurrency, said Patrick Gray, the Australian co-host and founder of the security news podcast Risky Business.
“I’ve seen a few people poo-poohing the sanctions…but the sanctions component is actually less important than the doxing component,” Gray said. “Because this guy’s life just got a lot more complicated. He’s probably going to have to pay some bribes to stay out of trouble. Every single criminal in Russia now knows he is a vulnerable 33 year old with an absolute ton of bitcoin. So this is not a happy time for him.”

