Table of Contents: Initial Vision and Founding Objectives Diverging Philosophies on Control and Governance Disagreements on Compensation and Recruitment The Microsoft Partnership Dispute Strategic Shifts: Nonprofit to Capped-Profit Structure Trust Issues and Board Dynamics Exit and Aftermath Released Emails From the Musk vs. Altman Case Subject: question (May 25, 2015 – Jun 24, 2015) Subject: […]
Cybersecurity researchers have flagged a surge in malware distribution tactics involving fake CAPTCHAs and counterfeit AI applications. This new wave of cyberattacks targets both Windows and macOS systems and is closely linked to malicious software strains like Lumma Stealer and AMOS. These malware types are notorious for their ability to collect sensitive user data, including […]
Bluesky’s evolution from a low-profile initiative within Twitter to a platform with over 18 million users, at the time of writing, highlights the rapidly changing dynamics in the social media world. The company surpassed one million daily new user registrations on November 15 for the first time, adding currently another million every day since then. […]
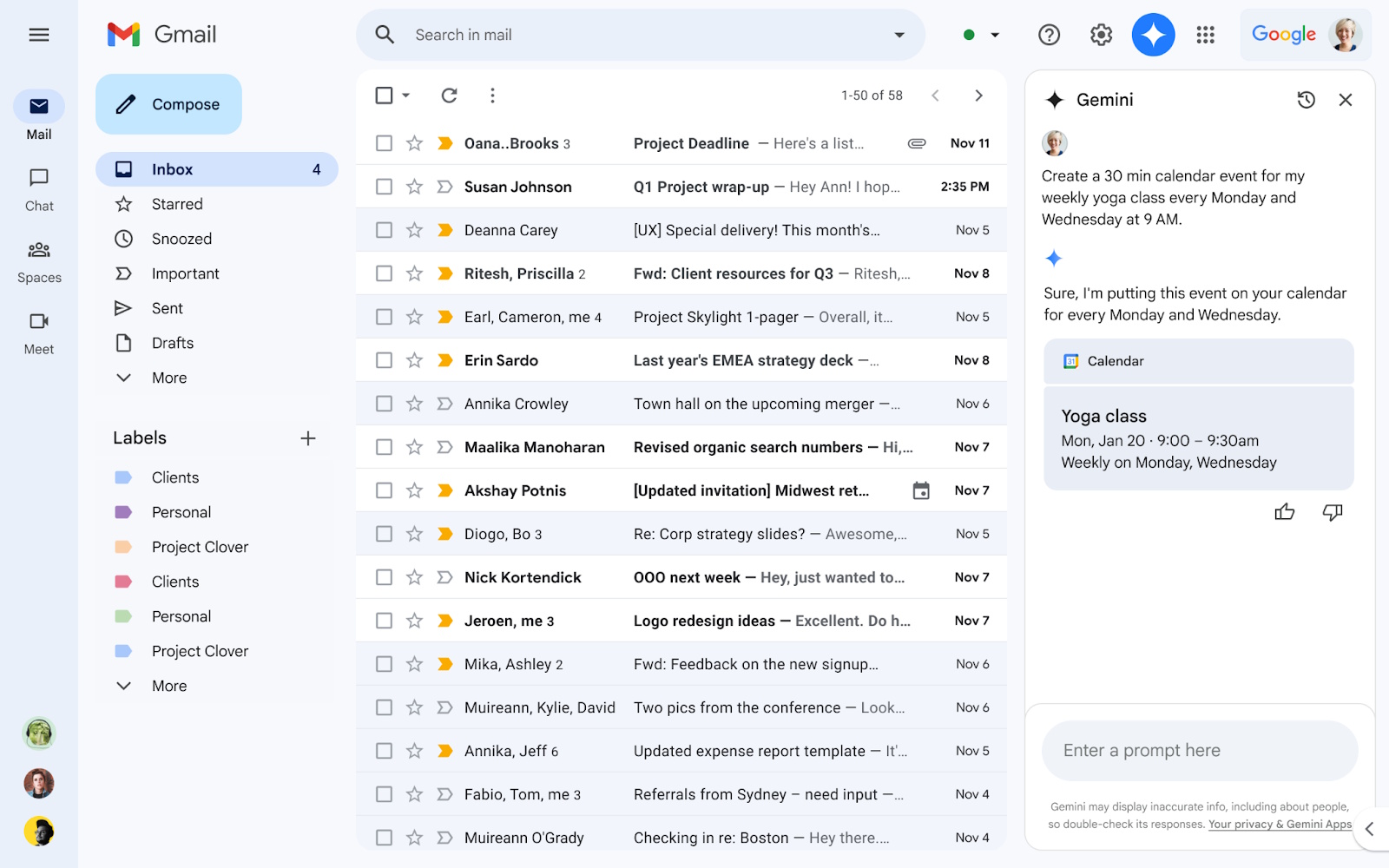
Google has updated its Workspace suite, bringing new capabilities to users of Docs and Gmail through Gemini AI. The improvements, aimed at enhancing productivity and user experience, introduce a tool for generating inline images in Google Docs and new Calendar integration directly within Gmail. New Image Creation Capabilities in Google Docs Google Docs users can […]
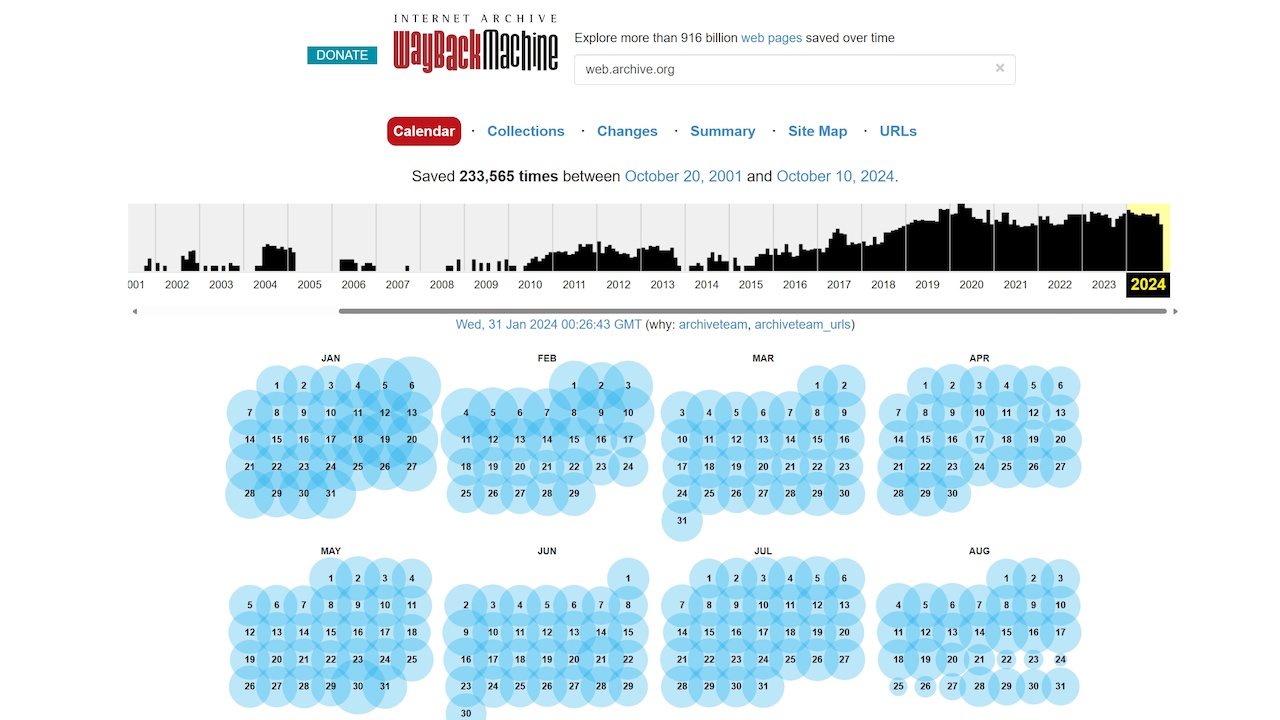
In the wake of severe cyberattacks that have threatened its services, the Internet Archive, known for its Wayback Machine and expansive digital resources, has been implementing major security measures. The recent wave of cyber incidents included a significant data breach in October 2024 that exposed the personal details of over 31 million accounts, such as […]
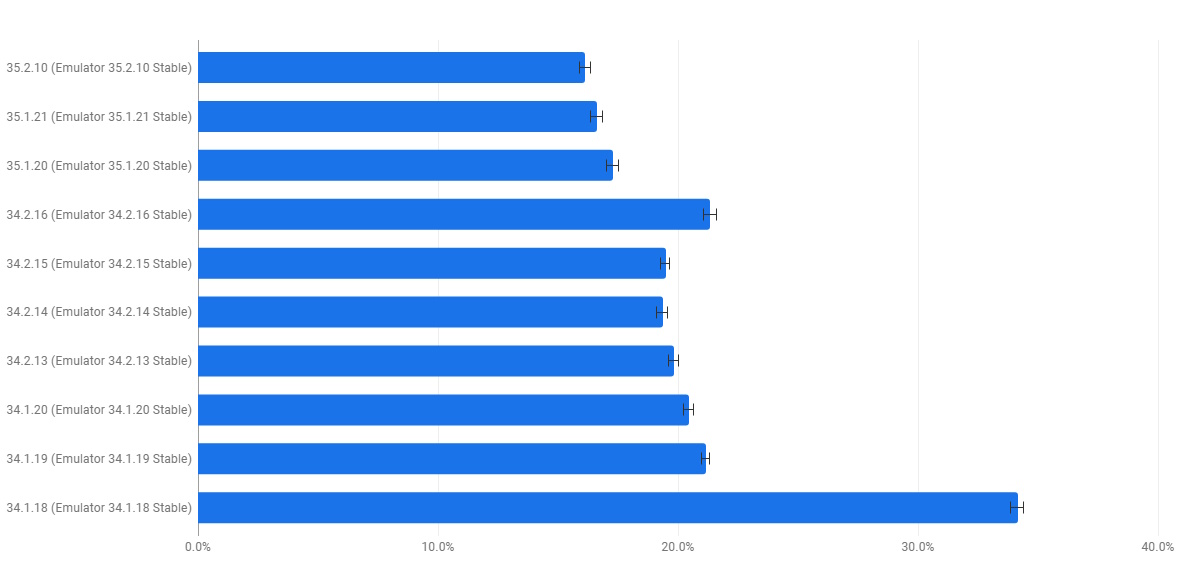
Google’s Android Studio team has rolled out significant updates to its Android Emulator this week, focusing on stability and performance under Project Quartz, a six-month initiative. The project shifted attention from adding new features to optimizing the core user experience, addressing developer frustrations tied to system crashes and slow performance. The latest improvements are accessible […]
Microsoft has taken a significant step for Windows 11 for Arm-based PCs by releasing an official ISO for download. The release not only simplifies the installation process for users and developers but also includes critical updates to the Prism emulator, enhancing its support for x64 applications with advanced instruction sets. Windows 11 on Arm ISO […]
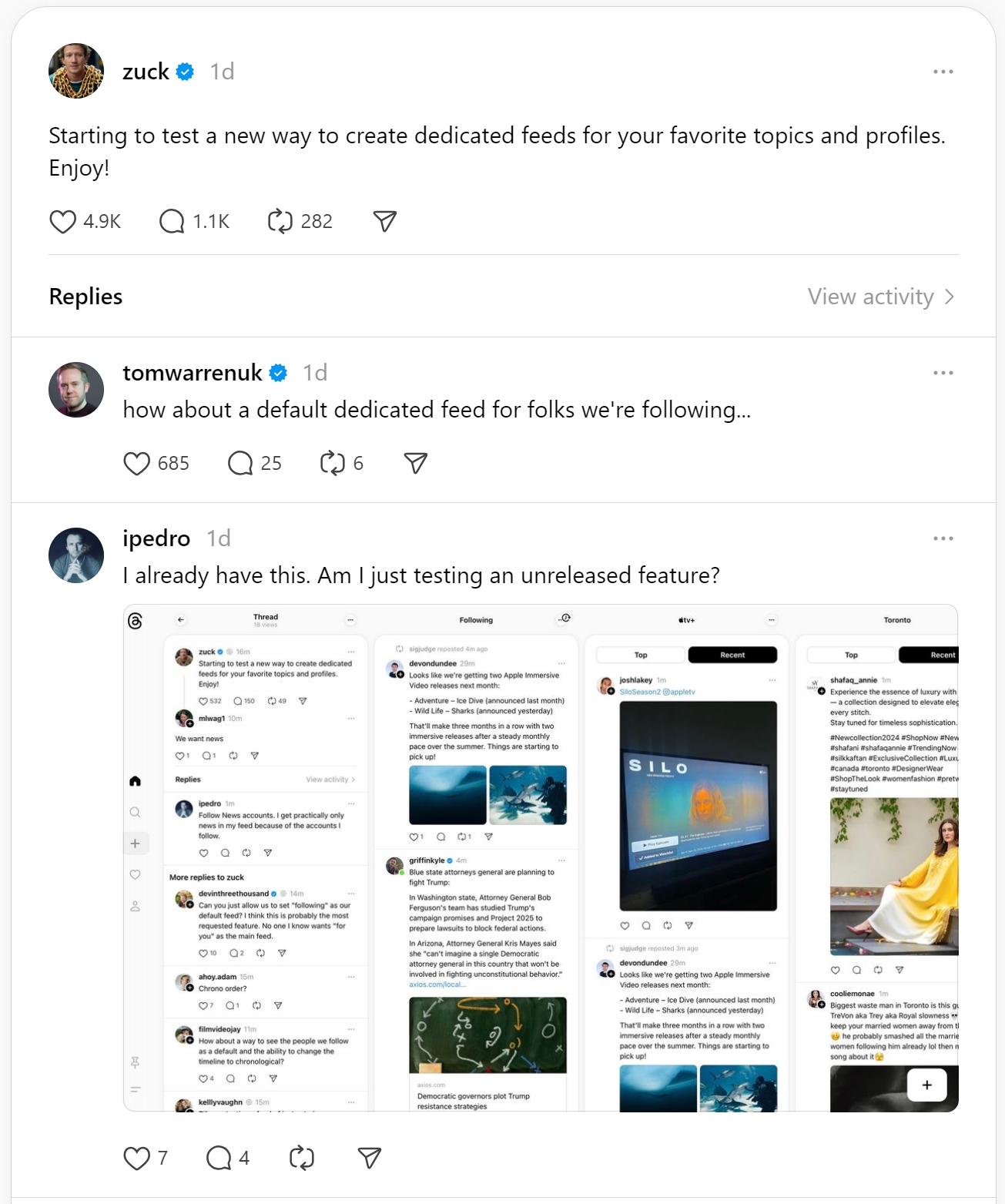
Meta is enhancing Threads, its alternative to X, by testing custom feeds that let users better manage their content. In addition, advertisements will be reportedly introduced starting January 2025, signaling Meta’s move to monetize the platform and align it with its other social media properties, Facebook and Instagram. Custom Feeds: Personalized Browsing for Users Threads […]
Newly released court filings have unveiled that Israeli surveillance firm NSO Group continued deploying malware exploits targeting WhatsApp, even during ongoing legal battles with Meta. Initiated in October 2019, a lawsuit by Meta accused NSO of facilitating spyware attacks that compromised around 1,400 devices, breaching federal and state laws, including the US Computer Fraud and […]
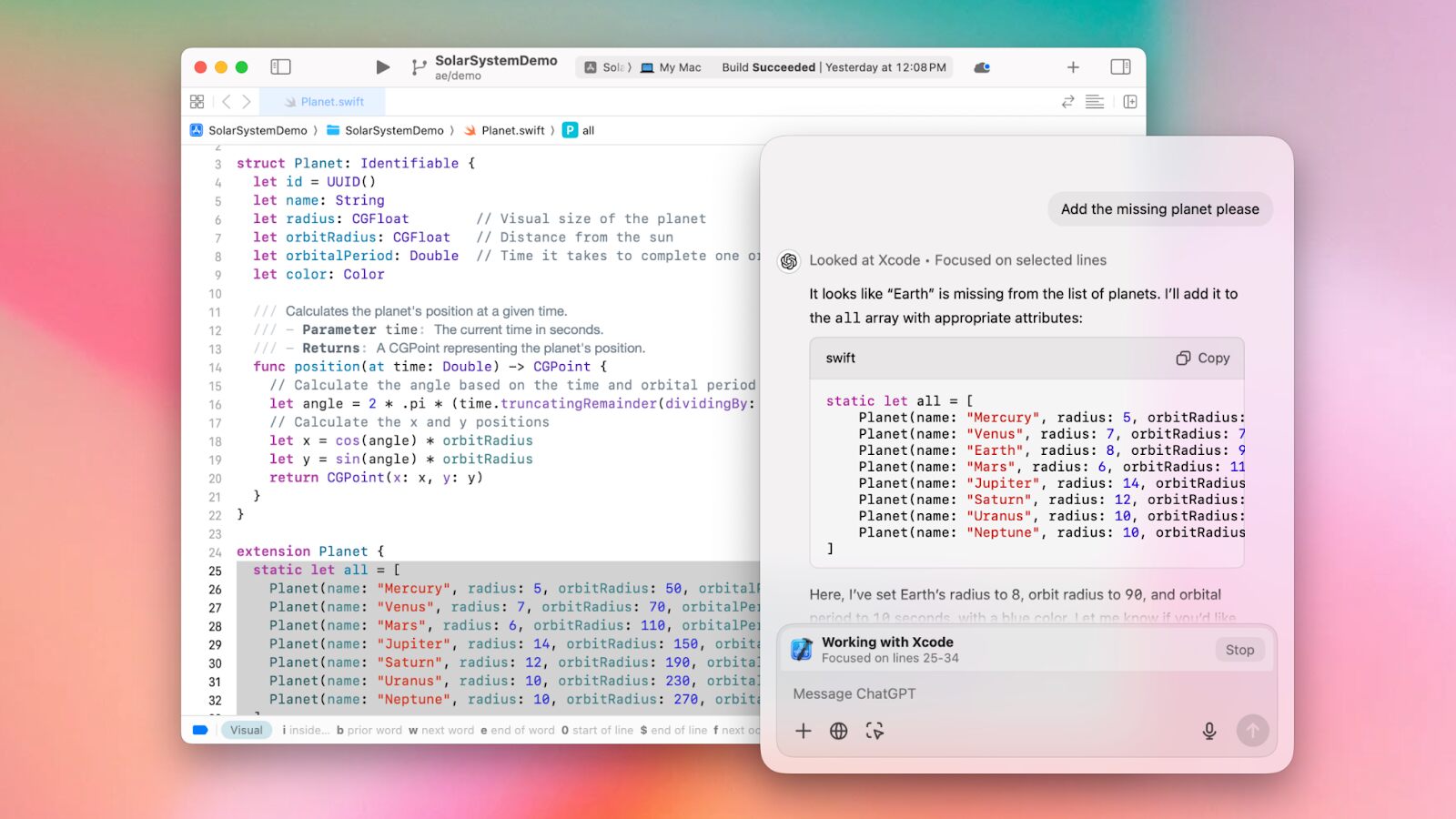
OpenAI has introduced an upgrade to its macOS ChatGPT app, integrating the AI tool with coding environments such as VS Code, Xcode, Terminal, and iTerm2. The new feature, named “Work with Apps,” enables ChatGPT to read active code within these applications, offering assistance without requiring users to copy and paste code snippets manually. “Work with […]